-
Japan develops anti-hacker weapon
The Japanese Ministry of Defense recently revealed that it is developing a new weapon to combat hackers – a “seek and destroy” virus designed to track and disable the source of cyber-attacks
-
-
ETrade cyberattack shuts down trading
Over the holiday season, Australia’s second-largest online brokering service, ANZ Bank’s ETrade was hit by a series of cyberattacks, temporarily locking out customers
-
-
Government contractors now required to have cybersecurity plans
Based on a new General Services Administration (GSA) rule, all contractors and subcontractors that provide federal agencies with IT services, systems, or supplies are required to submit a cyberescurity plan that matches government regulations
-
-
Signcryption technology tightens cybersecurity
Signcryption is a data security technology by which confidentiality is protected and authenticity is achieved seamlessly at the same time; it has now been formally recognized as an international standard by the International Organization of Standardization (ISO)
-
-
UMD, Lunarline partner on cybersecurity
The University of Maryland Cybersecurity Center will partner with Lunarline Inc. on cybersecurity education, research, and technology development
-
-
Wireless passwords vulnerable to hackers, US-CERT warns
The U.S. government is warning wireless users that their home and business networks are highly vulnerable to hackers
-
-
Smartphone users hold false sense of security
A recent study reveals that smartphone users maintain a false sense of cybersecurity
-
-
New Apple facial recognition tech could make passwords obsolete

Passwords could become a thing of the past for Apple iPhone and iPad users; the tech company recently revealed a patent application for what it is calling “Low Threshold Face Recognition,” a tool that would allow users to unlock their phones by simply picking up the device and pointing it at their face
-
-
McAfee releases 2012 cyber threat predictions

The cyberthreats organizations and individuals are likely to face in 2012 will resemble those they faces in 2011, only more so; among the increased threats: attacks on critical infrastructure, mobile devices and consumer electronics, and politically motivated attacks
-
-
DHS social media monitoring policy under fire
DHS’ tactics of gathering intelligence via social media has drawn sharp criticism from privacy advocates with one group filing a lawsuit against the department
-
-
Lieberman asks Twitter to shut down Taliban accounts

Senator Joe Lieberman (I-Connecticut), the chair of the Homeland Security Committee, has requested that the popular social media site Twitter shut down the accounts of the Taliban
-
-
DHS, Idaho lab win cybersecurity innovation award
The Controls Systems Security Program (CSSP) at DHS and Idaho National Laboratory have created a series of training programs for managerial and technical people in the critical infrastructure sector that are packed with up-to-date information on cyber threats and mitigations for vulnerabilities
-
-
Anonymous threatens Internet blackout over controversial legislation

The hacker group Anonymous has vowed to blackout the Internet if U.S. lawmakers pass the controversial Stop Online Piracy Act; under the bill, government powers would be greatly expanded, enabling the Justice Department working at the behest of individual copyright holders to shut down Web sites for potential copyright violations
-
-
Lawmaker targets fake ID smartphone app
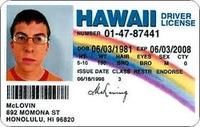
With the “License” app for Apple iPhones and iPads, making a realistic fake ID has never been easier; to prevent this app from falling into the wrong hands that would use it for nefarious purposes, Senator Bob Casey (D — Pennsylvania) recently requested that Apple remove the app from its online store
-
-
National Guardsmen, the new front line in cybersecurity

In an aggressive push to expand the military’s cyber warfare and defense capabilities, the National Guard has formed an increasing number of special cybersecurity units; National Guard cybertroops have proven to be particularly appealing solution, especially with defense cuts looming, as they cost less to train, maintain, and retain than active duty forces
-
More headlines
The long view
States Rush to Combat AI Threat to Elections
This year’s presidential election will be the first since generative AI became widely available. That’s raising fears that millions of voters could be deceived by a barrage of political deepfakes. Congress has done little to address the issue, but states are moving aggressively to respond — though questions remain about how effective any new measures to combat AI-created disinformation will be.
Ransomware Attacks: Death Threats, Endangered Patients and Millions of Dollars in Damages
A ransomware attack on Change Healthcare, a company that processes 15 billion health care transactions annually and deals with 1 in 3 patient records in the United States, is continuing to cause massive disruptions nearly three weeks later. The incident, which started on February 21, has been called the “most significant cyberattack on the U.S. health care system” by the American Hospital Association. It is just the latest example of an increasing trend.
Chinese Government Hackers Targeted Critics of China, U.S. Businesses and Politicians
An indictment was unsealed Monday charging seven nationals of the People’s Republic of China (PRC) with conspiracy to commit computer intrusions and conspiracy to commit wire fraud for their involvement in a PRC-based hacking group that spent approximately 14 years targeting U.S. and foreign critics, businesses, and political officials in furtherance of the PRC’s economic espionage and foreign intelligence objectives.
Autonomous Vehicle Technology Vulnerable to Road Object Spoofing and Vanishing Attacks
Researchers have demonstrated the potentially hazardous vulnerabilities associated with the technology called LiDAR, or Light Detection and Ranging, many autonomous vehicles use to navigate streets, roads and highways. The researchers have shown how to use lasers to fool LiDAR into “seeing” objects that are not present and missing those that are – deficiencies that can cause unwarranted and unsafe braking or collisions.
Tantalizing Method to Study Cyberdeterrence
Tantalus is unlike most war games because it is experimental instead of experiential — the immersive game differs by overlapping scientific rigor and quantitative assessment methods with the experimental sciences, and experimental war gaming provides insightful data for real-world cyberattacks.
