-
How the Heartbleed bug reveals a flaw in online security
The Heartbleed bug – which infects an extremely widespread piece of software called OpenSSL — has potentially exposed the personal and financial data of millions of people stored online has also exposed a hole in the way some security software is developed and used. The Heartbleed bug represents a massive failure of risk analysis. OpenSSL’s design prioritizes performance over security, which probably no longer makes sense. But the bigger failure in risk analysis lies with the organizations which use OpenSSL and other software like it. A huge array of businesses, including very large IT businesses with the resources to act, did not take any steps in advance to mitigate the losses. They could have chosen to fund a replacement using more secure technologies, and they could have chosen to fund better auditing and testing of OpenSSL so that bugs such as this are caught before deployment. They didn’t do either, so they — and now we — wear the consequences, which likely far exceed the costs of mitigation.
-
-
Hacked U.S. surveillance drone over Crimea shows new face of warfare

A recent report of a U.S. surveillance drone flying over the Crimea region of Ukraine being hacked by Russian forces, is just one of many indication that the twenty-first-century global battlefield will take place in cyberspace. Radio and other frequencies which cover the electromagnetic spectrum are the new contested domain.
-
-
British intelligence agency promotes cybersecurity education
As part of its national cybersecurity strategy to “derive huge economic and social value from a vibrant, resilient, and secure cyberspace,” the United Kingdom will issue certifications to colleges and universities offering advanced degrees in cybersecurity. The British intelligence agency, Government Communications Headquarters(GCHQ), has notified various institutions to apply for certification by 20 June 2014. Students who complete the approved courses will carry a “GCHQ-certified degree.”
-
-
How computer worms are spreading among smartphones
Researchers have recently discovered that some of the most common activities among smartphone users — scanning 2D barcodes, finding free Wi-Fi access points, sending SMS messages, listening to MP3 music, and watching MP4 videos — can leave devices vulnerable to harmful “computer worms.” These worms can infiltrate smartphones through apps designed in a specific computer language/code — and they can do more harm than just steal the device owner’s personal information, researchers warn. They can also spread to the owner’s friends and personal contacts.
-
-
Feds struggle to plug power grid security holes
Many of the current vulnerabilities in the power grid are attributable to newly adopted smart-grid technology, which allows operators to transmit energy from a diverse pool of resources. Smart-grid technology relies on devices in remote locations which constantly communicate with substations, those access points can be compromised by hackers.
-
-
DHS repairing internal security operations
Last week DHS announced plans to overhaul its security operations center (SOC), the organization which protects DHS’ internal networks, and deploy a Next Generation Enterprise Security Operations Center (NextGen ESOC) which will incorporate state-of-the-art SOC technologies, concepts, and capabilities to address future security needs.
-
-
Measuring smartphone malware infection rates
Researchers show that infection rates in Android devices at around 0.25 percent are significantly higher than the previous independent estimate. They also developed a technique to identify devices infected with previously unknown malware.
-
-
Student develops new way to detect hackers
A Binghamton U student and her teammates are working on developing a new hacking detection solution. Instead of reviewing all programs run by a network to find the signature of one of millions of known malware programs — some of which mutate to avoid detection — they have developed a technology to assess behavior of individual computers. This is done by monitoring system calls, the internal signals that accompany every computer operation and can reveal every function performed by the computer.
-
-
U.S. Cyber Challenge opens registration for Cyber Quests competition
Last week the Council on CyberSecurity, through the U.S. Cyber Challenge (USCC) initiative, announces the open registration of its qualifying Cyber Quests competition — a challenging online contest open to high school and college students, as well as professionals, who will compete against their peers across the country for an invitation to one of four Cyber Camps being offered this summer. The online competition and camps are designed to improve cybersecurity skills, provide training and mentorship from leading instructors and highlight skills for potential employers.
-
-
Inspired by nature, researches develop “unbreakable” security codes
A revolutionary new method of encrypting confidential information has been patented by scientists who have been inspired by their discoveries from human biology, which model how the heart and lungs coordinate their rhythms by passing information between each other. A mathematical model based on the complex interaction between these organs has now been transferred to the world of modern communications.
-
-
Making quantum cryptography suitable for mobile phones
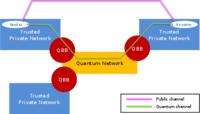
Secure mobile communications underpin our society and through mobile phones, tablets and laptops we have become online consumers. The security of mobile transactions is obscure to most people but is absolutely essential if we are to stay protected from malicious online attacks, fraud and theft. Researchers have shown how it is possible to make the resources necessary for quantum cryptography less bulky and expensive, and thus more suitable for mobile handsets.
-
-
Capabilities-based – rather than actuarial -- risk analysis would make businesses safer
Many businesses and organizations, when applying cost-benefit analysis and a risk-management analysis to measure cyber risk, are relying on the assumption that the likelihood of a future attack depends heavily on how many attacks have occurred in the past. Since there has yet to be a full-scale attack on critical infrastructure in the United States, it is simple to conclude that the risk of a cyberattack on critical infrastructure is low, therefore justifying low investment in additional security initiatives. An actuarial risk analysis may conclude that there is little likelihood of such as attack occurring, but a capabilities-based risk analysis recognizes that since adversaries are capable of such an attack, it is in an organization’s best interest to secure against it.
-
-
Cryptolocker has you between a back-up and a hard place

Cryptolocker, a particularly vicious form of malware that first appeared in September 2013, is a game-changer. After getting into your computer, it will encrypt all your data files, from your word documents to your photos, videos, and PDFs. It will then ask for a ransom of around $300 or 0.5 bitcoins to get them back. It has been one of the most commented developments in computer security circles in recent times, and copycats are appearing. The criminals are netting tens or hundreds of millions in ransoms, and at least some of the ill-gotten gains secured from Cryptolocker are likely to be reinvested. The criminals behind it will likely pay for access to bigger botnets to reach a wider base of victims. Future versions of the virus will in all likelihood be more prevalent and will extend across other platforms, like smartphones and tablets.
-
-
Delaware launches cyber initiative
Delaware is joining the number of states that have decided to invest in a statewide cybersecurity workforce to combat the growing threat of cyberattacks directed at both private and public institutions.Delaware hopes its cyber initiative will accelerate current efforts to develop a stronger cyber workforce. The Delaware Cyber Initiative proposes $3 million for a collaborative learning and research network in the form of part research lab, part business park, dedicated to cyber innovation.
-
-
Protecting personal data on smartphone
Social networking and the instantaneous sharing of information have revolutionized the way we communicate. Our mobile phones are able to automatically obtain information such as our current location and activities. This information can be easily collected and analyzed to expose our private life. What is even more malicious is that the personal data contained in our smartphones can be disclosed via installed applications without our being informed.
-
More headlines
The long view
Researchers Develop AI Agent That Solves Cybersecurity Challenges Autonomously
New framework called EnIGMA demonstrates improved performance in automated vulnerability detection using interactive tools.
