-
Cyphort, a threat monitoring specialist, raises $15.5 million Series B funding
San Jose, California-based Cyphort, Inc., a company specializing in advanced threat monitoring and mitigation platform, has closed in $15.5 million Series B funding. The round was led by Menlo Park, California-based Trinity Ventures with participation from existing investors Foundation Capital and Matrix Capital. Cyphort’s platform blends multi-phase behavioral analysis, machine learning, and correlation to provide businesses with real-time detection, context, and mitigation for advanced malware attacks that bypass traditional security and first generation APT solutions.
-
-
NIST seeks public comments on updated smart-grid cybersecurity guidelines
The National Institute of Standards and Technology (NIST) is requesting public comments on the first revision to its guidelines for secure implementation of “smart grid” technology. The draft document, NIST Interagency Report (IR) 7628 Revision 1: Guidelines for Smart Grid Cybersecurity, is the first update to NISTIR 7628 since its initial publication in September 2010.
-
-
DDoS protection specialist Black Lotus raises $3.5 million
San Francisco-based Black Lotus, a DDoS protection specialist, last week announced the completion of its first institutional financing in the amount of $3.5 million. The round was led by San Francisco-based Industry Capital. The strategic investment will fund entry into new markets, where Black Lotus will deploy additional capacity and improve quality of service through peering and closer proximity to global partner networks.
-
-
Terrorism insurance should cover cyberterrorism: industry
The Terrorism Risk Insurance Act(TRIA) is a federal backstop designed to protect insurers in the event an act of terrorism results in losses above $100 million. Industry officials question whether cyber terrorism is covered by the program, which is administered by the Treasury Department. Industry insiders note that terrorism risks have evolved since TRIA was enacted and cyberterrorism is now a real threat. TRIA should thus not simply be reauthorized with a blanket stamp of approval; instead there should be a discussion about whether acts of cyberterrorism should be explicitly included in TRIA.
-
-
NIST releases Preliminary Cybersecurity Framework
The National Institute of Standards and Technology (NIST) on Tuesday released its Preliminary Cybersecurity Framework to help critical infrastructure owners and operators reduce cybersecurity risks in industries such as power generation, transportation, and telecommunications. In the coming days, NIST will open a 45-day public comment period on the Preliminary Framework and plans to release the official framework in February 2014.
-
-
Violin Memory: Winning over the intelligence community
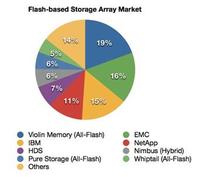
Violin Memory (NSYE: VMEM) is a recently IPO’d enterprise flash memory provider that has won installations across the most demanding branches of government, particularly in intelligence and homeland security. One advantage the company holds is a partnership with Toshiba, the world’s #2 manufacturer of NAND, which reportedly gives Violin insider-access to the unpublished R&D data, allowing for a product that has steadily performed steps ahead of the competition. The partnership also allows Violin to buy NAND at special “producer-like” prices from Toshiba, which in turn has enabled Violin to price more competitively, up to 50 percent lower than other providers. What is clear is that Violin’s technology adoption is growing exponentially within the security sector and other areas where data performance cannot be compromised and is mission critical.
-
-
Cybersecurity specialist Bromium raises $40 million Series C funding
Cupertino, California-based Bromium, Inc. has raised $40 million in an Series C funding round led by new investor Meritech Capital Partners, with participation from existing investors Andreessen Horowitz, Ignition Partners, Highland Capital Partners, and Intel Capital. Bromium offers advanced malware protection and automated forensic intelligence products. Bromium’s vSentry uses Intel CPU and chipset features to hardware-isolate tasks that access the Web, attachments, and files that might contain malware, protecting the desktop by design.
-
-
New apps to keep you healthy
For those wanting to keep their distance from health threats like E. coli-contaminated lettuce or the flu, there are two upcoming apps for that. The Department of Energy’s Pacific Northwest National Laboratory (PNNL) hosted a competition this summer in which graduate students designed two mobile apps to fight the threats of food-related illnesses and the flu. The apps are called FoodFeed and FL•U (pronounced “flu you”).
-
-
Cyber Grand Challenge for automated network security-correcting systems
What if computers had a “check engine” light that could indicate new, novel security problems? What if computers could go one step further and heal security problems before they happen? To find out, the Defense Advanced Research Projects Agency (DARPA) intends to hold the Cyber Grand Challenge (CGC) — the first-ever tournament for fully automatic network defense systems. The Challenge will see teams creating automated systems that would compete against each other to evaluate software, test for vulnerabilities, generate security patches, and apply them to protected computers on a network. The winning team in the CGC finals would receive a cash prize of $2 million, with second place earning $1 million and third place taking home $750,000.
-
-
Physicians feared terrorists might hack Dick Cheney’s cardiac defibrillator

In a 60 Minutes segment aired yesterday (Sunday), former vice-president Dick Cheney told the interviewer that his doctors turned off the wireless function of his implanted cardiac defibrillator (ICD) “in case a terrorist tried to send his heart a fatal shock.” Asked about the concern of Cheney’s physicians, electrophysiologists — these are the cardiologists who implant ICDs – say that as far as they know, this has never happened in the real world but that it is impossible to rule out the possibility.
-
-
Backlash: growing interest in counter-surveillance tools
The revelations about the NSA surveillance programs has prompted what some see as high-tech civil disobedience: a growing number of products and applications aiming to limit the NSA’s ability to access encrypted e-mails, obtain phone records, and listen to phone conversations.
-
-
U.K. launches cyberwarfare reserve force
U.K. defense secretary Philip Hammond announced that the Ministry of Defense (MoD) has begun this month to recruit the country’s top IT specialiststo join the Joint Cyber Reserve Unit (JCRU). “In response to the growing cyber threat, we are developing a full-spectrum military cyber capability, including a strike capability, to enhance the U.K.’s range of military capabilities,” Hammond said.
-
-
Bipartisan cybersecurity measure to be introduced in Congress
Senator Saxby Chambliss (R-Georgia) last week said he was “very close” to introducing legislation which would encourage the private sector and government agencies to share information regarding cyberattacks. Chambliss has proposed a government “portal,” operated by DHS, to handle information coming from the private sector. Privacy advocates welcome the proposal for a civilian agency like DHS to operate the information sharing “portal” (in earlier versions of proposed cybersecurity legislation, the NSA was tasked with a similar coordinating responsibility).
-
-
Web sites secretly track users without relying on cookies
Device fingerprinting, also known as browser fingerprinting, is the practice of collecting properties of PCs, smartphones, and tablets to identify and track users. For the vast majority of browsers, the combination of these properties is unique, and thus functions as a “fingerprint” that can be used to track users without relying on cookies. Researchers have discovered that 145 of the Internet’s 10,000 top Web sites use device fingerprinting to track users without their knowledge or consent.
-
-
Popular e-commerce software vulnerable to hackers
Online transactions rely on a trusted third party, or “cashier,” who bridges the gap between vendors and their customers. The use of a third party cashier, however, also complicates the payment logic and introduces a new class of vulnerabilities that can result in significant financial losses to merchants. Computer scientists found flaws in e-commerce software that allowed them to purchase stationery, candy, and toys online at below their correct cost.
-
More headlines
The long view
Researchers Develop AI Agent That Solves Cybersecurity Challenges Autonomously
New framework called EnIGMA demonstrates improved performance in automated vulnerability detection using interactive tools.
