-
Lawmakers seek to protect NY’s growing nanotech industry from terrorists
Last week during a Senate Judiciary Committee hearing, Senator Charles Schumer (D – New York) strongly urged DHS Secretary Janet Napolitano to secure New York’s growing nanotechnology industry against a Mexican terrorist group that has attacked nanotechnology firms around the world
-
-
Stuxnet-clones easily created

Initial reports regarding Stuxnet suggested that the code was developed by elite computer experts with the help of state support and highly secretive military intelligence, but security experts working in a laboratory setting have been able to recreate key elements of the worm in a short time frame with limited resources
-
-
Facebook facial recognition proving problematic overseas
A German court ruled that Facebook’s facial recognition software is in violation of German and European privacy laws; the company has until 7 November to amend its software to comply with German and EU laws or else it will face legal action
-
-
Anonymous targets child porn sites, releases names of 1,500 members
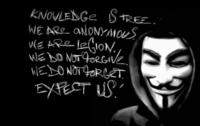
Last week hackers from the hacktivist movement Anonymous took down more than forty child pornography websites and leaked the names of more than 1,500 members that belonged to one of the sites Law enforcement officials may have a surprising new ally in the fight against child pornography and those who distribute it
-
-
Privacy flaws can reveal users’ identities, locations, and digital files
Researchers will soon notify Internet scholars of flaws in Skype and other Internet-based phone systems that could potentially disclose the identities, locations, and even digital files of the hundreds of millions of users of these systems
-
-
Army Reserve could soon take on homeland security missions

The House and the Senate are currently debating legislation that would allow the Army Reserve to be deployed for homeland security missions
-
-
Terrorism in Africa: Kenyan troops invade Somalia
On Wednesday, Kenya sent its troops some 100 miles inside Somalia to take the battle to the Islamic Al Shabaab organization, killing some 75 militants; yesterday, AU troops stormed a stronghold of Al Shabaab militant group on the outskirts of Mogadishu, while a militia backed by Kenyan troops simultaneously attacked another Shabaab stronghold along the Kenya-Somalia border, taking it over and forcing Shabab fighters to flee; Somalia’s nominal government relies on Ethiopian and Kenyan troops to fight Islamic terrorists in Somalia
-
-
Colorado reorganizes homeland security
On Wednesday the state of Colorado announced that it was reorganizing its homeland security operations
-
-
Also noted
Tennessee Becomes First State To Fight Terrorism Statewide | Scientists develop explosive disposal technology | Earthquakes in western U.S. May Raise Disaster Awareness | Insurance price surge in no-flood zones in Australia | MIT political scientist discusses border security | Some Cheer U.S.-Mexico Border Fence as Others Ponder the Cost | Plan to screen trucks may ease U.S.-Canada traffic
-
-
Google making search more secure
Google is enhancing its default search service for signed-in users; over the next few weeks, many users will find themselves redirected to https://www.google.com (note the extra “s”) when they are signed in to their Google account; this change encrypts their search queries and Google’s results page
-
-
Underage cartel recruits increasingly prosecuted by local courts
In the past when Border Patrol or Immigration and Customs Enforcement (ICE) agents would catch teenagers smuggling narcotics, the agency would hand the case over to federal prosecutors, but Border Patrol has entered into a new arrangement with local prosecutors and the U.S. Attorney General’s office to send cases directly to local courts for prosecution
-
-
Federal court blocks portions of Alabama immigration law
Last week a federal judge blocked enforcement of several provisions of a controversial Alabama immigration law
-
-
Qaddafi killed – 42-year rule over
There are reports from Libya that Col. Muamar Qaddafi was killed while trying to escape his besieged hometown of Sirte; NATO says that a convoy of several vehicles was attacked as it was trying to make its way out of the city, and that when rebel forces approached the destroyed cars, they found Col Qaddafi in one of the vehicles; there are conflicting reports about whether he was killed by NATO airstrike on the convoy, or killed by rebel forces which pulled him out of his car
-
-
GAO report: DHS data mining puts personal information at risk
A recent Government Accountability Office (GAO) report found that DHS and its sub-agencies do not properly protect personal information when conducting counterterrorism investigations
-
-
Arab Spring is different thing for different people
New research shows true picture of what and who is behind the political uprisings; although the idea of the “Arab Spring” is accepted by a large proportion of people in Arab countries, the reasons they are aligning themselves with it are very different and have grown more diverse the longer it has gone on
-
More headlines
The long view
Factories First: Winning the Drone War Before It Starts
Wars are won by factories before they are won on the battlefield,Martin C. Feldmann writes, noting that the United States lacks the manufacturing depth for the coming drone age. Rectifying this situation “will take far more than procurement tweaks,” Feldmann writes. “It demands a national-level, wartime-scale industrial mobilization.”
No Nation Is an Island: The Dangers of Modern U.S. Isolationism
The resurgence of isolationist sentiment in American politics is understandable but misguided. While the desire to refocus on domestic renewal is justified, retreating from the world will not bring the security, prosperity, or sovereignty that its proponents promise. On the contrary, it invites instability, diminishes U.S. influence, and erodes the democratic order the U.S. helped forge.
Fragmented by Design: USAID’s Dismantling and the Future of American Foreign Aid
The Trump administration launched an aggressive restructuring of U.S. foreign aid, effectively dismantling the United States Agency for International Development (USAID). The humanitarian and geopolitical fallout of the demise of USAID includes shuttered clinics, destroyed food aid, and China’s growing influence in the global south. This new era of American soft power will determine how, and whether, the U.S. continues to lead in global development.
Water Wars: A Historic Agreement Between Mexico and US Is Ramping Up Border Tension
By Natasha Lindstaedt
As climate change drives rising temperatures and changes in rainfall, Mexico and the US are in the middle of a conflict over water, putting an additional strain on their relationship. Partly due to constant droughts, Mexico has struggled to maintain its water deliveries for much of the last 25 years, deliveries to which it is obligated by a 1944 water-sharing agreement between the two countries.
How Disastrous Was the Trump-Putin Meeting?
In Alaska, Trump got played by Putin. Therefore, Steven Pifer writes, the European leaders and Zelensky have to “diplomatically offer suggestions to walk Trump back from a position that he does not appear to understand would be bad for Ukraine, bad for Europe, and bad for American interests. And they have to do so without setting off an explosion that could disrupt U.S.-Ukrainian and U.S.-European relations—all to the delight of Putin and the Kremlin.”
How Male Grievance Fuels Radicalization and Extremist Violence
By Haily Tran
Social extremism is evolving in reach and form. While traditional racial supremacy ideologies remain, contemporary movements are now often fueled by something more personal and emotionally resonant: male grievance.
