-
Preparing your organization for Stuxnet-like attack
A cybersecurity expert describes Stuxnet as “this epochal change”; he says that although Stuxnet was of such complexity and required such significant resources to develop that few attackers will be in a position to produce a similar threat in the near future, we now know that the dangers of Stuxnet-like threats are no longer theoretical
-
-
Russian bloggers fall victim to cyber attacks
Earlier this month LiveJournal, a major Russian blogging site, was the victim of a large cyber attack; bloggers believe that it was a move meant to silence political dissent in advance of the country’s elections; the site was brought down by a distributed denial of service (DDos) attack; SUP, the owners of LiveJournal, said that the recent attacks were the worst in its company’s history and unprecedented in that it targeted the entire website rather than individual blogs; the majority of Russia’s opposition leaders and political activists maintain blogs on LiveJournal that they use as platforms to gain support and spread their message
-
-
Iran admits Stuxnet's damage
A senior Iranian official admitted that the Stuxnet malware, which infected tens of thousands of computers and servers used in Iran’s nuclear weapons complex inflicted serious damage on Iran’s nuclear program, including large-scale accidents and loss of life
-
-
Chips may sabotage hi-tech weapons
Countries producing sophisticated weapon systems do not want these systems to fall into the wrong hands; one idea is to plant a chip in these weapons which would allow the country that supplied them to destroy or disable them remotely; already there are worries that with chip manufacturing moving outside the United States, foreign powers may bribe or coerce chip manufacturers into planting “backdoor” circuits in chips these manufacturers sell American defense contractors
-
-
Call for creating a U.S. cybersecurity emergency response capability
Lawmakers call for the creation of a cybersecurity emergency response capability to help businesses under major cyber attacks; “Who do you call if your CIO is overwhelmed, if you’re a local bank or utility?” Senator Sheldon Whitehouse (D-Rhode Island) asked; “How can we preposition defenses for our critical infrastructure, since these attacks come at the speed of light?”
-
-
Contradictions in U.S. cybersecurity policy
The United States wants a secure cyberspace, but its intelligence agencies have found enormous utility in using their own computer hacking capabilities to collect confidential information from foreign adversaries; this raises the question of how the U.S. government can push for global cybersecurity while at the same time using cyber means to collect intelligence on potentially threatening regimes such as Iran
-
-
CyberCom commander calls for government protection of critical infrastructure

General Keith Alexander, the head of the U.S. Cyber Command, is calling for the creation and implementation of a government strategy to protect critical infrastructure in the United States from cyber attacks; in a speech yesterday, General Alexander emphasized the importance of securing critical infrastructure like the stock market, the electrical grid, and power plants against cyber attacks; he sought to ease fears by assuring the audience that the government could protect critical infrastructure and preserve civil liberties; Alexander’s remarks come as civil rights advocates and internet freedom groups have grown more vociferous in their criticism of a recent Senate bill that would help secure the nation’s critical infrastructure from cyber attacks; supporters of the bill say that it is impossible to create an internet “kill switch” and that is not their goal
-
-
Defining cyber warfare
Several high-profile cyberattack incidents lead commentators to worry that we may be using the wrong metaphor to describe the phenomena; Bruce Schneier, for example, says that “What we are seeing is not cyber war but an increasing use of war-like tactics and that is what is confusing us. We don’t have good definitions of what cyber war is, what it looks like and how to fight it”
-
-
Hackers release Stuxnet's decompiled code online
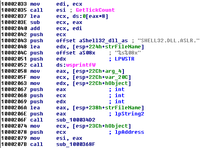
The Stuxnet worm was a cybermissile designed to penetrate advanced security systems; it was equipped with a warhead that targeted and took over the controls of the centrifuge systems at Iran’s uranium processing center in Natanz, and it had a second warhead that targeted the massive turbine at the nuclear reactor in Bushehr; security experts say it is the most sophisticated cyberweapon ever designed; now, a group of anonymous “hacktivists” hacked the computers of a U.S. security company and stole a decrypted version — the decompiled code — of the malware, and put it on the Web; security experts are anxious: “There is the real potential that others will build on what is being released,” says one; this will not lead to an immediate threat, but it could lead to something soon, he added; “Weeks wouldn’t surprise me”
-
-
Egypt's Internet blackout revives U.S. "kill switch" debate
Egypt’s five-day shutdown of the Internet has revived debate in the United States over how much authority the U.S. president should have over the Web in the event of a crisis; a bill pending before Congress would give the president the authority to shut down parts of the Internet in the event of a national security crisis such as a sustained enemy cyberattack on the U.S. national grid or financial systems; critics say this is a threat to civil liberties; “It’s not an Internet kill switch,” says one cyber expert; “But you can think about isolating certain domains or certain enterprises; say a big power company gets infected— You say to them, ‘Disconnect yourself before you infect other power companies’; It’s like an avian flu quarantine for the Internet”
-
-
Stuxnet may turn Bushehr into a new Chernobyl
The destructive Stuxnet virus infected some 45,000 industrial control computers and servers in Iran; it destroyed more than 20 percent of Iran’s centrifuges, and, on 16 November, forced Iran to shut down uranium enrichment operations; it also infected the control system of the Bushehr reactor; Stuxnet is a sophisticated virus: while doing its destructive work, it makes sure that control computers continue to display “normal” operational information; one Russian expert described how engineers at Bushehr “saw on their screens that the systems were functioning normally, when in fact they were running out of control”; a new intelligence report says that with control systems disabled by the virus, an accident in the reactor is likely — an accident which would have the force of a “small nuclear bomb”
-
-
Stuxnet heralds age of cyber weapons, virtual arms race
Mounting evidence indicates that Stuxnet was created by the United States and Israel to target Iran’s nuclear program; analysts call this the first use of a specially designed cyber weapon and fear the beginning of a cyber weapons arms race; one analyst hopes that a doctrine of mutually assured destruction will limit the use of these devastating weapons in the future; current trends and other analysts indicate that cyber space will continue to be militarized
-
-
NATO networks vulnerable to cyber threat: U.S.
U.S. says NATO’s military networks are not fully protected against cyber threats and the alliance must make good on a pledge to erect a virtual wall by 2012; U.S. Deputy Defence Secretary William Lynn warned at the end of a two-day visit to Brussels that the cyber threat was “maturing” from an espionage and disruption tool to a destructive force against vital infrastructure
-
-
Bill giving president power over Internet in cyber emergency to return
A controversial bill handing President Obama power over privately owned computer systems during a “national cyberemergency,” and prohibiting any review by the court system, will return this year; the bill which emerged from a Senate committee on 15 December 2010, is more restrictive in three respects than the original bill, made public June 2010: The revised version sayis that the federal government’s designation of vital Internet or other computer systems “shall not be subject to judicial review”; another addition expanded the definition of critical infrastructure to include “provider of information technology”; a third authorized the submission of “classified” reports on security vulnerabilities
-
-
Fears of cyberwar exaggerated: report
New report says that analysis of cyber-security issues has been weakened by the lack of agreement on terminology and the use of exaggerated language; the report says online attacks are unlikely ever to have global significance on the scale of, say, a disease pandemic or a run on the banks; the authors say, though, that “localized misery and loss” could be caused by a successful attack on the Internet’s routing structure, which governments must ensure are defended with investment in cyber-security training
-
- All
- Regional
- Water
- Biometrics
- Borders/Immig
- Business
- Cybersecurity
- Detection
- Disasters
- Government
- Infrastructure
- International
- Public health
- Public Safety
- Communication interoperabillity
- Emergency services
- Emergency medical services
- Fire
- First response
- IEDs
- Law Enforcement
- Law Enforcement Technology
- Military technology
- Nonlethal weapons
- Nuclear weapons
- Personal protection equipment
- Police
- Notification /alert systems
- Situational awareness
- Weapons systems
- Sci-Tech
- Sector Reports
- Surveillance
- Transportation
Advertising & Marketing: advertise@newswirepubs.com
Editorial: editor@newswirepubs.com
General: info@newswirepubs.com
2010-2011 © News Wire Publications, LLC News Wire Publications, LLC
220 Old Country Road | Suite 200 | Mineola | New York | 11501
Permissions and Policies
Editorial: editor@newswirepubs.com
General: info@newswirepubs.com
2010-2011 © News Wire Publications, LLC News Wire Publications, LLC
220 Old Country Road | Suite 200 | Mineola | New York | 11501
Permissions and Policies
