-
Researching cyber vulnerabilities in computer-controlled cars may violate copyright law
The advent of computer controlled, Internet-capable vehicles is offering fertile new ground to hackers. Groups of “white hat” hackers have already demonstrated the vulnerabilities inherent in the new cars’ computer systems – by taking control over a car from ten miles away. One problem in addressing the issue is that the control software is proprietary, and is owned by the developers, and researching it to uncover flaws may be a violation of copyright laws.
-
-
Vulnerabilities found in use of certificates for Web security
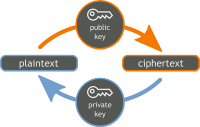
Consumers use the Internet for banking, e-mailing, shopping, and much more nowadays. With so much personal and private information being transmitted over the Web, Internet users must be able to rely on and trust the sites they are accessing. For security purposes, Web sites use certificates to establish encrypted communications. When a site becomes compromised, its certificate should be revoked. Astudy finds that Web site administrators are providing a large number of revoked certificates, certificate authorities are not using newer processes for distributing revocations, and Web browsers are not checking whether certificates have been revoked.
-
-
Stealing encryption keys on Amazon’s Cloud servers

Cloud computing is a service that enables companies and organizations to store information and run computer applications without making their own investments in actual computer hardware or employing IT staff. Researchers have demonstrated that RSA encryption keys, which are used by thousands of companies and organizations to protect the data and processes they entrust to cloud-based services, can be obtained using a sophisticated side-channel attack — despite recent efforts by cloud service providers and cryptography software developers to eliminate such vulnerabilities.
-
-
U.S. fears a Russian attack on undersea internet cables that could plunge world into chaos
It may sound far-fetched at first, but there’s a growing fear of the damage a newly aggressive Russia might inflict in a time of tension or conflict simply by damaging or cutting the undersea cables that carry almost all of the West’s Internet traffic. The perfect global cyberattack could involve severing the fiber-optic cables at some of their hardest-to-access locations in order to halt the instant communications on which the West’s governments, military, economies and citizens have grown dependent. Effectively this would cripple world commerce and communications, destabilize government business and introduce uncertainty into military operations. A significant volume of military data is routed via this Internet backbone. If Russia’s investment in information warfare is any measure we should be concerned — this investment in information warfare is not being matched by the United States and Europe combined.
-
-
Identifying students cognitively equipped to succeed in cybersecurity
The University of Maryland Center for Advanced Study of Language (CASL) will partner with the U.S. Air Force to conduct a two-year study designed to advance the cyber workforce. The Air Force says that by assessing abilities rather than knowledge, it will broaden its cyber pipeline while improving outcomes and maintaining a highly skilled workforce.
-
-
PNNL to help DHS address critical infrastructure vulnerabilities
The Department of Energy’s Pacific Northwest National Laboratory (PNNL) has been named a supporting laboratory to the National Infrastructure Simulation and Analysis Center (NISAC). NISAC is a Department of Homeland Security (DHS) program which addresses the potential vulnerabilities and consequences of disruption of U.S. critical infrastructure. PNNL says it will contribute advanced computer modeling and simulation capabilities to look at the dependencies, interdependencies, vulnerabilities, and complexities of important critical infrastructure sectors such as dams, water, transportation, energy, and information technology.
-
-
Better understanding of how computer users detect malware and phishing attacks
Detecting malware and phishing attacks are user-centered functions, but little is understood about the user behavior underlying these tasks. Researchers have conducted a study that provides new insights on users’ susceptibility to, and capability to detect, cyber-criminal attacks such as malware and phishing attacks. The study analyzed users’ brain activity and eye gaze movements as they were subjected to these attacks.
-
-
Amendment to CISA: U.S. courts could pursue foreigners for crimes abroad against other foreigners
A controversial amendment to an already-controversial cybersecurity bill will allow U.S. courts to pursue, convict, and jail foreign nationals in cases in which these foreigners committed crimes against other foreigners on foreign soil. The amendment to the Cybersecurity Information Sharing Act (CISA) cleared a key Senate hurdle on Thursday. It aims to lower the barrier for prosecuting crimes committed abroad.
-
-
EFF leads privacy advocates in opposing CISA
Privacy advocates have intensified their campaign against the Cybersecurity Information Sharing Act (CISA), which the Senate will vote on sometime next week. The Electronic Frontier Foundation (EFF) says it vehemently opposes the bill, as well as amendments which would expand the Computer Fraud and Abuse Act. EFF says that CISA is fundamentally flawed. The bill’s broad immunity clauses, vague definitions, and what EFF describes as “aggressive spying powers” combine to “make the bill a surveillance bill in disguise.”
-
-
Ruling shows Europe still vexed over NSA spying, leaving U.S. companies in legal limbo
For over fifteen years, the Data Transfer Pact between the European Union and the United States, more commonly known as Safe Harbor, had ensured that companies with EU operations could transfer online data about their employees and customers back to the United States despite stark differences between U.S. and European privacy law. Earlier this month, U.S. companies operating in Europe got some unwelcome news: Safe Harbor had been ruled invalid. The European court’s ruling has serious implications for these companies’ business models and profitability, leaving many scrambling to find solutions. But it also exposes a fundamental cultural rift between the U.S. and Europe’s conceptions of privacy – one that a new agreement won’t be able to paper over.
-
-
New tool allows users to see how their personal information is used on the Web
Navigating the Web gets easier by the day as corporate monitoring of our e-mails and browsing habits fine-tune the algorithms that serve us personalized ads and recommendations. But convenience comes at a cost. In the wrong hands, our personal information can be used against us, to discriminate on housing and health insurance, and overcharge on goods and services, among other risks. “The Web is like the Wild West,” says one researcher. “There’s no oversight of how our data are being collected, exchanged and used.”
-
-
Identifying stealth attacks on complicated computer systems
Imagine millions of lines of instructions. Then try and picture how one extremely tiny anomaly could be found in almost real-time and prevent a cyber security attack. A trio of Virginia Tech computer scientists has tested their “program anomaly detection approach” against many real-world attacks.
-
-
Cyberthreats, cyberattattacks will only increase over time: Experts
The increasing dependency of a growing number of organizations on the Internet has served to increase the number of targets for hackers, particularly those organizations that have not given adequate attention to securing their network as they should. Even those networks not connected to the Internet are not immune from penetration by hackers. This is a threat that shows no sign of ever slowing down. More likely it will only increase over time, as cyber-capabilities are developed by more and more entities.
-
-
Guarding networks from “insider threats”
Even the best-protected, most sensitive computer networks resemble castles: They have walls to ward off outside threats, but their interiors are full of weak points. This is why the “insider threat” — someone within a system who, out of malice or naiveté puts a system at risk - -is considered one of the most serious risks in the cybersecurity world. “The insider threat is clearly a challenge for organizations, because most countermeasures were developed for external attacks,” says one researcher.
-
-
Grid Security Conference focuses on information sharing among stakeholders
More than 300 industry and federal partners are participating in the North American Electric Reliability Corporation’s (NERC) annual grid security conference, or GridSecCon, in Philadelphia, which opened on Wednesday and ends today. The conference is focusing on key cyber and physical security issues and training for enhancing the security and resiliency of the North American bulk power system. Topics of panel discussions include upgrades to NERC’s E-ISAC, cyber and physical security technology options, the transition to Version 5 of NERC’s critical infrastructure protection standards; and expectations for NERC’s third grid security exercise, GridEx III, which takes place 18-19 November.
-
More headlines
The long view
Researchers Develop AI Agent That Solves Cybersecurity Challenges Autonomously
New framework called EnIGMA demonstrates improved performance in automated vulnerability detection using interactive tools.
