-
N.Y. State Police app helps citizens report suspicious activity
The New York State Police is urging citizens to download a new digital app which allows citizens to capture and report suspicious activity with their smart phones. The app is part of the “See Something, Send Something” campaign which aims to turn willing citizens into the eyes and ears of law enforcement. For example, if a citizen notices an unattended package at a train station of an airport, they could use the app to alert law enforcement.
-
-
Tech companies: weakening encryption would only help the bad guys
Leading technology companies — Apple, Microsoft, Google, Samsung, Twitter, Facebook, and fifty-six other technology companies — have joined forces to campaign against weakening end-to-end encryption, insisting that any weakening of encryption would be “exploited by the bad guys.” Apple’s chief executive Tim Cook recently asserted that “any backdoor is a backdoor for everyone.”
-
-
DHS runs many unsecured databases: IG
DHS Inspector General found that DHS is running dozens of unpatched databases, some of which are rated “secret” and even “top secret.” An audit of the department’s IT infrastructure has found large security gaps, including the fact that 136 systems had expired “authorities to operate” – that is, no one was in charge of keeping them updated. Of the 136, 17 were classified as “secret” or “top secret.”
-
-
E-mail security is better than it was, but far from perfect
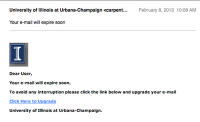
E-mail security helps protect some of our most sensitive data: password recovery confirmations, financial data, confidential correspondences, and more. A new report finds that e-mail security is significantly better than it was two years ago, but still has widespread issues.
-
-
Encryption firm tightens access following Paris attacks
Encrypted communications specialist Silent Circle, after learning that ISIS was recommending two of the company’s products — the encrypted Blackphone handset and Silent Phone applications for private messaging — to the organization’s followers, is taking steps to make it more difficult for terrorists and their followers to use these products.
-
-
Telegram IM app recalibrates policies after Paris attacks
Pavel Durov, the creator of the popular instant messaging app Telegram, has said that following the Paris terrorist attacks, his company has blocked dozens of accounts associated with the jihadist Islamic State group. As is the case with other technology companies, Telegram is trying to negotiate the balance between privacy and security: the same privacy-enhancing technology which keeps customers’ communication private, also helps terrorists communicate with each other and plot attacks safe from monitoring and surveillance by intelligence agencies and law enforcement.
-
-
Paris terrorist attacks reignite debate over end-to-end encryption, back doors
The exact way the terrorists who attacked France last Friday communicated with each other, and their handlers, in the run-up to the attack is not yet clear, but the attack has prompted law enforcement and intelligence agencies in Europe and the United States to renew their call to regulate the use of new encryption technologies which allow users to “go dark” and make it difficult, if not altogether impossible, to retrieve the contents of communication.
-
-
Forge-proof authentication method to revolutionize security
Scientists have discovered a way to authenticate or identify any object by generating an unbreakable ID based on atoms. The technology uses next-generation nanomaterials to enable the unique identification of any product with guaranteed security. uses atomic-scale imperfections which are impossible to clone as they comprise the unmanipulable building blocks of matter. The researchers used atomic-scale imperfections which are impossible to clone as they comprise the unmanipulable building blocks of matter.
-
-
Iranian global cyber espionage campaign exposed
Check Point Software Technologies Ltd. on Monday published a 38-page report identifying specific details and broad analysis on cyber-espionage activity conducted by the group “Rocket Kitten,” with possible ties to Iranian Revolutionary Guard Corps. The new report also reveals details of the group’s global operations and insight into more than 1,600 of their targets.
-
-
Automated application whitelisting to prevent intrusions, malware
Automated application whitelisting regulates what software can load onto an organization’s network. It is one of a number of techniques that can help prevent malware infections, and it complements other security technologies that are part of an enterprise’s defense-in-depth resources. The National Institute of Standards and Technology (NIST) has published a guide to deploying automated application whitelisting to help thwart malicious software from gaining access to organizations’ computer systems.
-
-
DHS S&T-funded technology protects devices from cyberattacks
In 2011, a small group of university researchers working on securing embedded devices caught the attention of the Department of Homeland Security (DHS) Science and Technology Directorate (S&T). That effort has since evolved into a one-of-a-kind technology — called Symbiote — which Hewlett-Packard (HP) recently licensed from Red Balloon Security, to protect its printers from cyberattacks.
-
-
Iran Revolutionary Guard hackers target State Department’s Iran-policy personnel
Hackers working for Iran’s Revolutionary Guards have in recent weeks intensified their hacking campaign against e-mail and social media accounts of Obama administration officials. U.S. officials say they believe the cyberattacks are linked to the arrest in Tehran of an Iranian-American businessman. The cyberattacks appear to target people working on Iran policy, with many of attacks focusing on personnel in the State Department’s Office of Iranian Affairs and the Bureau of Near Eastern Affairs.
-
-
NSF highlights more than forty years of supporting cybersecurity research and education

New report highlights NSF-funded cybersecurity research and education. Today, NSF invests nearly $160 million each year in interdisciplinary research, education, and workforce development help protect national and personal security. This support helps scientists develop the tools, training, and people that will keep the nation safe and maintain online privacy.
-
-
In our Wi-Fi world, the internet still depends on undersea cables
Not many people realize that undersea cables transport nearly 100 percent of transoceanic data traffic. These lines are laid on the very bottom of the ocean floor. They’re about as thick as a garden hose and carry the world’s Internet, phone calls and even TV transmissions between continents at the speed of light. A single cable can carry tens of terabits of information per second. The cables we all rely on to send everything from e-mail to banking information across the seas remain largely unregulated and undefended. Any single cable line has been and will continue to be susceptible to disruption. And the only way around this is to build a more diverse system, because the thing that protects global information traffic is the fact that there’s some redundancy built into the system. But as things are, even though individual companies each look out for their own network, there is no economic incentive or supervisory body to ensure the global system as a whole is resilient. If there’s a vulnerability to worry about, this is it.
-
-
Protecting vehicles from cyberattacks

The Department of Homeland Security (DHS) Science and Technology Directorate (S&T) has awarded two grants for the development of technologies that can help defend government and privately owned vehicles from cyberattacks. “Modern vehicles are no longer purely mechanical systems,” said Dr. Dan Massey, S&T Cyber Physical Systems Security (CPSSEC) Program Manager. “Today’s vehicles have interdependent cyber components used for telematics, conveniences, and safety-critical systems. A stealthy adversary could gain access to a vehicle’s cyber components and remain completely hidden until initiating a widespread attack.”
-
More headlines
The long view
Researchers Develop AI Agent That Solves Cybersecurity Challenges Autonomously
New framework called EnIGMA demonstrates improved performance in automated vulnerability detection using interactive tools.
