-
A dandelion-shaped device to help in demining operations
Decades of war have left land mines buried all over the Afghan countryside; they continue to go off, killing and maiming hundreds of innocent people every year; last year alone, more than 812 people were wounded or killed in Afghanistan because of mines left behind after the armies retreated; two Afghan inventors designed a dandelion-like device for demining operations
-
-
U.S. troops arrive in Turkey to man missile defense batteries

Turkey, a NATO member, has asked the organization for missile defense battaeries to protect it against a possible attack by Syria; the United States, Germany, and the Netherland deployed Patriot missile batteries along the Syrian-Turkish border, with their nationals manning the weapons; U.S. troops arrived in Turkey on Friday to supervise the U.S.-supplied missiles
-
-
Unmanned vessel for continuous tracking of enemy submarines
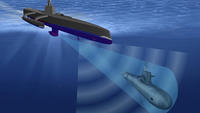
DARPA looking for an unmanned naval vessel that can seek out and track quiet diesel submarines, forcing them to return to base and thus protecting friendly ships from attack
-
-
Flexible electronics to make night vision more accurate, easier to use
For soldiers and first responders, having accurate, high-resolution imaging capabilities may mean the difference between success and failure; electrical and computer engineers set out to make night vision more accurate and easier for soldiers, pilots, and first responders to use
-
-
Flexible electronics to make night vision more accurate, easier to use
For soldiers and first responders, having accurate, high-resolution imaging capabilities may mean the difference between success and failure; electrical and computer engineers set out to make night vision more accurate and easier for soldiers, pilots, and first responders to use
-
-
Comparing boost-phase to non-boost-phase ballistic missile defense

An expert panel set forth to provide an assessment of the feasibility, practicality, and affordability of U.S. boost-phase missile defense compared with that of the U.S. non-boost missile defense when countering short-, medium-, and intermediate-range ballistic missile threats
-
-
Four-legged robotic mule now voice-controlled

DARPA researchers demonstrated new advances in the Legged Squad Support System (LS3) four-legged robot’s control, stability, and maneuverability, including “Leader Follow” decision making, enhanced roll recovery, exact foot placement over rough terrain, the ability to maneuver in an urban environment, and verbal command capability
-
-
Maintaining robust communications in congested and contested environments
Radios are used for a wide range of tasks, from the most mundane to the most critical of communications, from garage door openers to military operations’ as the use of wireless technology proliferates, radios and communication devices often compete with, interfere with, and disrupt the operations of other devices; a new DARPA challenge is looking for innovative approaches that ensure robust communications in such congested and contested environments
-
-
U.S. Defense Secretary signs order to deploy anti-missile units in Turkey

Secretary of Defense Leon Panetta on Friday signed an official deployment order to send 400 American military personnel as well as two Patriot air defense units to Turkey as the cross-border tensions between Turkey and Syria have increased
-
-
Deployable RF data backbone which matches fiber optic capacity
DARPA envisions 100-Gigabit per second RF communications link between airborne and ground assets; the goal is for the data link to achieve a range greater than 200 kilometers between airborne assets and a range greater than 100 kilometers between an airborne asset (at 60,000 feet) and the ground
-
-
High Russian official: Assad losing the ground war
The Assad regime does not have many friends left, and yesterday one of them admitted that Assad was losing the war; Mikhail Bogdanov, the deputy foreign minister of Russia, said the regime faced possible defeat to the rebels, adding with unusual frankness for a diplomat: “One must look facts in the face”
-
-
U.S. Navy scientists honored for significant portfolio of newly patented discoveries and inventions

U.S. Navy scientists and engineers in 2012 once again had the world’s most significant government portfolio of newly patented discoveries and inventions, according to a November report published by the Institute of Electrical & Electronics Engineers (IEEE)
-
-
Climate change, water shortage play only secondary role in causing conflict – at least so far
Intelligence services and militaries around the world have been talking about, and preparing for, the danger of “water wars” and about climate change as a threat to national security; the results of an EU-funded research project, however, found that such discourses oversimplify a complex reality; climate and water resource changes are important, but play only a secondary role — at least for the time being — in the causation of conflict and insecurity compared to political, economic, and social factors
-
-
Top U.S., Canadian officials meet to discuss quickening pace of Arctic changes

One manifestation of global warming is the accelerating pace of Arctic ice-cap melting; the U.S. Navy Arctic Roadmap, authored by the Navy’s Task Force Climate Change, notes that, “Because the Arctic is primarily a maritime environment, the Navy must consider the changing Arctic in developing future policy, strategy, force structure and investment”; top U.S. and Canadian officials meet to discuss the implications of the rapidly melting arctic ice
-
-
Syria military launches Scud missiles at rebels
Facing growing political isolation, deteriorating economic conditions, and military setbacks, the Assad regime is escalating the level of violence in its war against the opposition; the three latest weapons the regime used in its effort to hold off the rebels: Scud missiles, cluster bombs, and incendiary munitions; yesterday, Pakistan became the 69th country to close its embassy in Damascus
-
More headlines
The long view
Factories First: Winning the Drone War Before It Starts
Wars are won by factories before they are won on the battlefield,Martin C. Feldmann writes, noting that the United States lacks the manufacturing depth for the coming drone age. Rectifying this situation “will take far more than procurement tweaks,” Feldmann writes. “It demands a national-level, wartime-scale industrial mobilization.”
