EncryptionStealing encryption keys on Amazon’s Cloud servers
Cloud computing is a service that enables companies and organizations to store information and run computer applications without making their own investments in actual computer hardware or employing IT staff. Researchers have demonstrated that RSA encryption keys, which are used by thousands of companies and organizations to protect the data and processes they entrust to cloud-based services, can be obtained using a sophisticated side-channel attack — despite recent efforts by cloud service providers and cryptography software developers to eliminate such vulnerabilities.
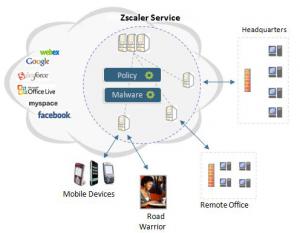
Schematic of ZScaler's security design // Source: commons.wikimedia.org
Researchers at Worcester Polytechnic Institute (WPI) have demonstrated that RSA encryption keys, which are used by thousands of companies and organizations to protect the data and processes they entrust to cloud-based services, can be obtained using a sophisticated side-channel attack — despite recent efforts by cloud service providers and cryptography software developers to eliminate such vulnerabilities.
The research was described in a paper published in the International Association for Cryptologic Research’s Cryptology ePrint Archive by a team led by Berk Sunar, professor of electrical and computer engineering, and Thomas Eisenbarth, assistant professor of electrical and computer engineering.
WPI reports that the team, supported by a $500,000 award from the National Science Foundation (NSF), used a combination of techniques to first create a virtual machine (essentially a remote computer running on a cloud server) on the same server as a target machine (a technique known as co-location). They then used the co-located machine to spy on the target. By observing how it accessed information in memory, they could determine when it was retrieving its RSA key (the code that protects data from unauthorized access). Finally, by charting the timing of the memory access they were able to deduce the key’s actual numeric sequence.
“We believe this is the first report in the cryptography literature to describe a successful RSA key recovery attack in a commercial cloud environment,” Sunar said.
Cloud computing is a service that enables companies and organizations to store information and run computer applications without making their own investments in actual computer hardware or employing IT staff. Instead, the cloud providers maintain large arrays of computer servers that users access through the Internet. Using the cloud instead of investing in dedicated hardware makes it easier and less expensive for companies to scale up their operations. In fact, the cloud has helped enable the rapid expansion of companies like Netflix and Dropbox.
