CybersecurityA new world for hackers: Acoustic side-channel attack
During the DNA synthesis process in a laboratory, recordings can be made of the subtle, telltale noises made by synthesis machines. And those captured sounds can be used to reverse-engineer valuable, custom-designed genetic materials used in pharmaceuticals, agriculture and other bioengineering fields.
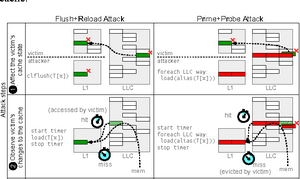
Schematic illustration of side-channel attacks // Source: semanticscholar.org
Researchers from the University of California, Irvine and the University of California, Riverside have uncovered the possibility of an acoustic side-channel attack on the DNA synthesis process, a vulnerability that could present a serious risk to biotechnology and pharmaceutical companies and academic research institutions.
“A few years ago, we published a study on a similar method for stealing blueprints of objects being fabricated in 3-D printers, but this attack on DNA synthesizers is potentially much more serious,” said Mohammad Al Faruque, UC Irvine associate professor of electrical engineering and computer science. “In the wrong hands, DNA synthesis capability could result in bioterrorists synthesizing, at will, harmful pathogens such as anthrax.”
Al Faruque said his lab’s discovery might also be used for a good cause: “Government agencies can employ the same technique as a monitoring tool to nullify the possibility of such activities.”
Listening in
A DNA synthesizer is a complex machine with meandering pipes, fluid reservoirs, solenoid valves and electrical circuitry. Chemicals — which have their own unique acoustic signatures due to their varying densities — flow through tubes, creating distinct noises punctuated by the clicking of valves and the whirring of pressure pump motors.
“All of these inner workings of a DNA synthesizer result in the emission of subtle but distinguishable sound signatures that can give clues as to the specific genetic material being generated,” said Sina Faezi, a UC Irvine graduate student in electrical engineering and computer science, who will present a paper on the potential threat of an acoustic side attack on DNA synthesizers at the Network & Distributed System Security Symposium taking place Feb. 24-27 in San Diego.
He said that in many cases, variances in the sounds produced are so tiny that people can’t distinguish them. “But through careful feature engineering and a bespoke machine learning algorithm written in [Al Faruque’s] lab, we were able to pinpoint those differences,” he said.
