-
Hackers working for a “state actor” planted spyware in WhatsApp via missed calls
Hackers, in all likelihood working for a state, managed to circumvent WhatsApp security by exploiting vulnerability associated with missed calls. The hackers planted an advanced spying software created by Israeli cyber company NSO to infect a few dozen phones. WhatsApp said the attack bore “all the hallmarks of a private company known to work with governments to deliver spyware that reportedly takes over the functions of mobile phone operating systems.”
-
-
Russia has Americans’ weaknesses all figured out
What are Americans supposed to think when their leaders contradict one another on the most basic question of national security—who is the enemy? Is Russia the enemy, or was the investigation of Russia’s interference in the 2016 election just a slow-motion attack on the president and his supporters? Are Russian fake-news troll farms stirring up resentment among the American electorate, or are mainstream-media outlets just making things up? Jim Sciutto writes in Defense One that U.S. military commanders, national-security officials, and intelligence analysts have a definitive answer: Russia is an enemy. It is taking aggressive action right now, from cyberspace to outer space, and all around the world, against the United States and its allies. But the public has been slow to catch on, polls suggest, and Trump has given Americans little reason to believe that their president recognizes Russia’s recent actions as a threat.
-
-
Report reveals scale of Russian interference in European democracy

Evidence of the Kremlin-backed Internet Research Agency’s long-term interest in European politics and elections has been revealed in two new studies. while Russian involvement in the 2016 U.S. presidential election has been well documented, far less has been known about the Internet Research Agency’s European operations, until now.
-
-
Hysteria over Jade Helm exercise in Texas was fueled by Russians, former CIA director says

Gov. Greg Abbott’s decision in 2015 to ask the Texas State Guard to monitor a federal military exercise prompted significant criticism. A former CIA director said Wednesday that the move emboldened Russians to next target elections.
-
-
U.S. official: Executive order not needed to ban Huawei in U.S. 5G networks

“We have grave concerns about the Chinese vendors because they can be compelled by the National Intelligence Law in China as well as other laws in China to take actions that would not be in the interests of the citizens of other countries around the world. Those networks could be disrupted or their data could be taken and be used for purposes that would not be consistent with fundamental human rights in those countries,” says Robert Strayer, deputy assistant secretary of state for cyber and international communications and information policy.
-
-
Breaking down the anti-vaccine echo chamber
In these days of Facebook and Twitter, it is easy enough to block out the opinions of those you disagree with, and only associate with people whose voices reinforce your own opinions. These echo chambers have real-world implications; currently, the U.S. is in the midst of its largest measles outbreak in decades. That’s why it’s important to find ways to communicate across the vaccination divide.
-
-
Electricity grid cybersecurity will be expensive – who will pay, and how much?

Russia, China, North Korea and Iran are capable of hacking into the computers that control the U.S. electricity grid. Protecting the grid from hacking would cost tens of billions of dollars. The electricity customers will likely foot most of the bill.
-
-
Crossing a cyber Rubicon?
Amid a massive exchange of rocket fire and airstrikes between Israel and both Hamas and Islamic Jihad this weekend, Hamas attempted a cyber operation against an unspecified civilian target in Israel. The operation failed, and in its aftermath the Israel Defense Forces carried out an airstrike that destroyed the building housing Hamas’s cyber capability. Some observers are citing the incident as an important—and perhaps dangerous—precedent. Others are questioning the legality of the strike itself. Robert Chesney writes in Lawfare that both these views are misplaced.
-
-
Facebook removes more pages, accounts linked to “inauthentic” Russian operators

Facebook said it has removed more pages and accounts that are believed to have originated in Russia and were involved in “coordinated inauthentic behavior.”
-
-
Agents of deceit: Russian disinformation institutions and actors
There is a burgeoning Western literature on Russian policy and practice in disinformation, but very little of it has detailed and reliable material about the government agencies and affiliated actors that promote it. A new, detailed report investigates the institutions and actors involved in Russian disinformation.
-
-
Blockchains are being exploited by bots for profit

Blockchains have been hailed as fair and open, constructed so a single user can’t falsify or alter records because they’re all part of a transparent network. The reality is not so simple, according to new research.
-
-
Flaws in metrics for user login systems

How good is the research on the success or failure of the system that verifies your identity when you log into a computer, smartphone or other device? Chances are it’s not good, and that’s a major security and privacy issue that should be fixed.
-
-
Why do some people believe the Earth is flat?
Why, despite overwhelming scientific evidence to the contrary, is the flat-Earth movement gaining traction in the twenty-first century? One expert says that, in part, it is due to a general shift toward populism and a distrust in the views of experts and the mainstream media. There is an “increasing distrust in what we once considered to be the gatekeepers of knowledge – like academics, scientific agencies, or the government,” she says. In this kind of environment, “it becomes really easy for once-fringe views to gain traction.”
-
-
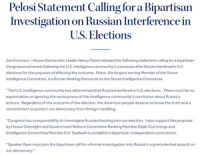
The Russia investigation will continue
Special Counsel Robert Mueller’s Russia probe is over, but the FBI is almost certain to continue its counterintelligence investigation into Russian espionage efforts related to the 2016 election. The FBI will continue to search for Americans working on behalf of the Kremlin. John Sipher writes in The Atlantic that the inability to establish that the Trump campaign conspired in a “tacit or express” agreement with the Russian government is not surprising. Most espionage investigations come up empty unless and until they get a lucky break. That does not mean there was no espionage activity in relation to the 2016 election. Every previous Russian political-warfare campaign was built on human spies. Russian “active measures”—propaganda, information warfare, cyberattacks, disinformation, use of forgeries, spreading conspiracies and rumors, funding extremist groups and deception operations—rely on human actors to support and inform their success. Counterintelligence professionals must doubt that Russia could have pulled off its election-interference effort without the support of spies burrowed into U.S. society or institutions.
-
-
Russia’s long game: Paralyze Europe’s ability to act in its own self-interest
With the European parliamentary elections approaching in less than a month’s time, Russia’s persistent disinformation campaign to subvert and undermine Europe’s democratic institutions is a source of growing worry. Russia is playing a long game in Europe: its objective is not merely to influence the outcome of any particular election, but rather to broadly subvert the efficacy of Europe’s democratic institutions, fuel widespread social fragmentation and mistrust, and ultimately paralyze Europe’s ability to act in its own self-interest and to defend our values.
-
More headlines
The long view
States Rush to Combat AI Threat to Elections
By Zachary Roth
This year’s presidential election will be the first since generative AI became widely available. That’s raising fears that millions of voters could be deceived by a barrage of political deepfakes. Congress has done little to address the issue, but states are moving aggressively to respond — though questions remain about how effective any new measures to combat AI-created disinformation will be.
Ransomware Attacks: Death Threats, Endangered Patients and Millions of Dollars in Damages
By Dino Jahic
A ransomware attack on Change Healthcare, a company that processes 15 billion health care transactions annually and deals with 1 in 3 patient records in the United States, is continuing to cause massive disruptions nearly three weeks later. The incident, which started on February 21, has been called the “most significant cyberattack on the U.S. health care system” by the American Hospital Association. It is just the latest example of an increasing trend.
Chinese Government Hackers Targeted Critics of China, U.S. Businesses and Politicians
An indictment was unsealed Monday charging seven nationals of the People’s Republic of China (PRC) with conspiracy to commit computer intrusions and conspiracy to commit wire fraud for their involvement in a PRC-based hacking group that spent approximately 14 years targeting U.S. and foreign critics, businesses, and political officials in furtherance of the PRC’s economic espionage and foreign intelligence objectives.
Autonomous Vehicle Technology Vulnerable to Road Object Spoofing and Vanishing Attacks
Researchers have demonstrated the potentially hazardous vulnerabilities associated with the technology called LiDAR, or Light Detection and Ranging, many autonomous vehicles use to navigate streets, roads and highways. The researchers have shown how to use lasers to fool LiDAR into “seeing” objects that are not present and missing those that are – deficiencies that can cause unwarranted and unsafe braking or collisions.
Tantalizing Method to Study Cyberdeterrence
By Trina West
Tantalus is unlike most war games because it is experimental instead of experiential — the immersive game differs by overlapping scientific rigor and quantitative assessment methods with the experimental sciences, and experimental war gaming provides insightful data for real-world cyberattacks.
