-
Florida GOP operative asked for – and received -- Russian hackers’ help in congressional race
The Wall Street Journal reports today that the Russian government hackers’ effort to upend the 2016 presidential election was not limited to stealing Democratic National Committee (DNC) and Clinton campaign emails and memos and then using Wikileaks to publish them in order to embarrass and weaken Hillary Clinton. Aaron Nevins, a Republican operative in Florida, now admits that he colluded with Russian government hackers in order to help the candidate he supported win a congressional race. When the Journal asked Nevins whether it was right to collaborate with the Russian government to undermine a congressional race in the United States, he responded: “If your interests align,” he said, “never shut any doors in politics.”
-
-
Network traffic offers early indication of malware infection
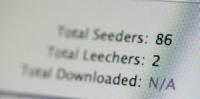
By analyzing network traffic going to suspicious domains, security administrators could detect malware infections weeks or even months before they’re able to capture a sample of the invading malware, a new study suggests. The findings point toward the need for new malware-independent detection strategies that will give network defenders the ability to identify network security breaches in a more timely manner.
-
-
Combination of features creates new android vulnerability
A new vulnerability affecting Android mobile devices results not from a traditional bug, but from the malicious combination of two legitimate permissions that power desirable and commonly-used features in popular apps. The combination could result in a new class of attacks, which has been dubbed “Cloak and Dagger.”
-
-
Russia may have rigged Brexit vote – and U.K.’s 8 June general election could be next: Experts
A report handed to the British Parliament’s Intelligence and Security Select Committee suggests that Russian secret funds and disinformation campaign may have swayed the EU referendum vote in favor of Brexit. Ahead of the 8 June parliamentary election, GCHQ [Government Communications Headquarters – the U.K. equivalent of the U.S. NSA] has warned leaders of Britain’s political parties of the threat Russian government hacking was posing to British democracy – while Russian interference with Brexit is also on the radar of the Electoral Commission, which is worried about the transparency of money donated to political parties and campaigns.
-
-
New funding enables work on Internet policy and cybersecurity for key infrastructure
MIT’s cross-disciplinary Internet Policy Research Initiative (IPRI) announced that it has awarded $1.5 million to a select group of principal investigators for early-stage Internet policy and cybersecurity research projects. “Understanding the nuance of cybersecurity risk in our critical infrastructure will help policymakers assure that the proper incentives are in place to reduce the threat of catastrophic attacks,” says IPRI founding director Daniel Weitzner.
-
-
Experts expect a surge in ransomware attacks this week – this time without a “kill switch”

A second version of the disruptive WannaCry ransomware – a version which does not contain the “kill switch” used by a young security analyst to shut down many of last week’s cyberattacks – is set to be released by the same group of hackers. There are fears that Monday could see a surge in the number of computers taken over by the devastating WannaCry ransomware hack. Rob Wainwright, head of the European Union police agency, Europol, warned anyone who thought the problem was going away was mistaken. “At the moment, we are in the face of an escalating threat. The numbers are going up, I am worried about how the numbers will continue to grow when people go to work and turn (on) their machines on Monday morning,” he said.
-
-
NHS ransomware cyber-attack was preventable

In a matter of hours, the NHS was effectively placed on lockdown with computer systems being held ransom and further machines powered down to prevent the spread of malware. Critical patient information has been inaccessible and several hospitals urged people to avoid accident and emergency departments, except in cases of real emergencies. But it is not just British infrastructure that has been affected by the ransomware. A total of 99 countries have suffered from this attack so far. Modern anti-virus software and up-to-date operating systems can only do so much. It is therefore vital to invest more in cyber-security training for all staff working with sensitive information. This attack proves that the UK’s cybers-security policy needs further work.
-
-
Educating, strengthening the cybersecurity workforce
As Americans become more dependent on modern technology, the demand to protect the nation’s digital infrastructure will continue to grow. CSU, designated as Centers of Academic Excellence in Information Assurance by the NSA and DHS, says that in an effort to produce career-ready cybersecurity professionals and to combat cybercrime nationwide, the California State University is creating educational opportunities for students and faculty members.
-
-
U.K. hospitals, clinics hit by large-scale ransomware cyberattack
The NHS has confirmed that hospitals across England have been hit by a large-scale cyberattack. The attack has locked staff out of their computers and forced emergency patients to be diverted to hospitals not hit by the attack. The IT systems of NHS facilities across England have been hit simultaneously – and the screens of computers connected to the networks under attack showed a pop-up message demanding a ransom in exchange for allowing staff access to the PCs.
-
-
DHS S&T’s Transition to Practice program unveils 2017 cohort
Eight new cybersecurity technologies developed by researchers at federally funded laboratories and academic research centers are ready for the commercial market. DHS S&T’s Transition to Practice (TTP) program will showcase its 2017 cohort 16 May in Washington. D.C.
-
-
New executive order on cybersecurity highlights need for deterrence, protection of key industries
President Trump’s new executive order on cybersecurity for federal computer networks and key elements of the country’s infrastructure – such as the electricity grid and core communications networks – builds meaningfully on the work of the Obama administration. Cybersecurity is ultimately an exercise in risk management. Given the range of possible threats and the pace at which they may appear, it is impossible to protect everything, everywhere, all the time. But it is possible to make sure that the most valuable resources (such as particular networks and systems, or specific data) are properly protected by, at minimum, good cyber-hygiene – and ideally, more. Overall, the order is a solid document, with guidance that is both measured and clear. Key to its success – and ultimately to the country’s security in cyberspace – will be the relationship the government builds with private industry. Protecting the country won’t be possible without both groups working in tandem.
-
-
Bypassing encryption: “Lawful hacking” is the next frontier of law enforcement technology
The discussion about how law enforcement or government intelligence agencies might rapidly decode information someone else wants to keep secret is – or should be – shifting. One commonly proposed approach, introducing what is called a “backdoor” to the encryption algorithm itself, is now widely recognized as too risky to be worth pursuing any further. The scholarly and research community, the technology industry and Congress appear to be in agreement that weakening the encryption that in part enables information security – even if done in the name of public safety or national security – is a bad idea. Backdoors could be catastrophic, jeopardizing the security of billions of devices and critical communications. A lawful hacking approach offers a solution that appears to gain greater favor with experts than encryption backdoors. A group of scholars proposed some ways we should begin thinking about how law enforcement could hack. Agencies are already doing it, so it’s time to turn from the now-ended debate about encryption backdoors and engage in this new discussion instead.
-
-
Cyber Security R&D Showcase coming in July
The 2017 Cyber Security R&D Showcase and Technical Workshop is scheduled for 11-13 July at Washington, D.C.’s Mayflower Hotel. In all, fifteen research areas will be featured: mobile security, cyber-physical system security, software assurance, data privacy, identity management, distributed denial of service defense, next generation cyber infrastructure, technology transition, cyber risk economics, cybersecurity research infrastructure, modeling of internet attacks, support for law enforcement, moving-target defense, cloud security and insider threats. During the conference, attendees can choose from more than 115 technical presentations representing a combined $250 million of federally funded R&D.
-
-
New meter to change how users create passwords
One of the most popular passwords in 2016 was “qwertyuiop,” even though most password meters will tell say it is a weak choice. The problem is that no existing meters offer any good advice to make it better — until now. Researchers have unveiled a new, state-of-the-art password meter that offers real-time feedback and advice to help people create better passwords. To evaluate its performance, the team conducted an online study in which they asked 4,509 people to use the meter to create a password.
-
-
Why we choose terrible passwords, and how to fix them

The first Thursday in May is World Password Day, but don’t buy a cake or send cards. Computer chip maker Intel created the event as an annual reminder that, for most of us, our password habits are nothing to celebrate. Instead, they – and computer professionals like me – hope we will use this day to say our final goodbyes to “qwerty” and “123456,” which are still the most popular passwords. So no more excuses. Let’s put on our party hats and start changing those passwords. World Password Day would be a great time to ditch “qwerty” for good, try out a password manager and turn on multi-factor authentication. Once you’re done, go ahead and have that cake, because you’ll deserve it.
-
More headlines
The long view
What Does Netflix’s Drama “Adolescence” Tell Us About Incels and the Manosphere?
While Netflix’s psychological crime drama ‘Adolescence’ is a work of fiction, its themes offer insight into the very real and troubling rise of the incel and manosphere culture online.
Confronting Core Problems in Cybersecurity
It’s common for governors and mayors to declare a state of emergency and activate the National Guard in the aftermath of hurricanes, tornadoes, and other natural disasters. But last month, officials in Minnesota took these steps in the wake of a major cyberattack on the city of St. Paul —a testament to how disruptive these attacks have become.
Voting from Your Sofa Is Secure Enough – but Will It Be Allowed?
A new electronic voting system developed at NTNU can withstand attacks from quantum computers, meaning digital elections can be conducted securely, even in the future.
