-
NIST removes cryptography algorithm from random number generator recommendations
Following a public comment period and review, the National Institute of Standards and Technology (NIST) has removed a cryptographic algorithm from its draft guidance on random number generators. Before implementing the change, NIST is requesting final public comments on the revised document, Recommendation for Random Number Generation Using Deterministic Random Bit Generators. The revised document retains three of the four previously available options for generating pseudorandom bits needed to create secure cryptographic keys for encrypting data. It omits an algorithm known as Dual_EC_DRBG, or Dual Elliptic Curve Deterministic Random Bit Generator.
-
-
SEC to examine robustness of Wall Street’s cyber defenses
The Security and Exchange Commission (SEC) announced plans last week to inspect the cyber defenses of fifty Wall Street investment advisers, brokers, and dealers to determine whether the financial sector is prepared for pinpointed cyberattacks. This is the first time the cybersecurity has made the list of the SEC’s annual investigations.
-
-
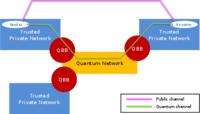
Major step toward stronger encryption technology announced
Researchers the other day announced the first successful trial of Quantum Key Distribution (QKD) technology over a live “lit” fiber network. The trial paves the way for more advanced research into QKD, the next frontier of data encryption technology, which will deliver even greater levels of network security.
-
-
Businesses looking to bolster cybersecurity
Since the recent data breaches at retailers Target and Neiman Marcus, in which hackers stole millions of customers’ credit and debit card information, consumers have been urging card providers to offer better secure payment processors. Legislators have introduced the Data Security Act of 2014 to establish uniform requirements for businesses to protect and secure consumers’ electronic data. The bill will replace the many different, and often conflicting, state laws that govern data security and notification standards in the event of a data breach.
-
-
West Point wins Cyber Defense Exercise, launches Army Cyber Institute
The U.S. Military Academy at West Point has won the annual Cyber Defense Exercise (CDX) which brought together senior cadets from the five service academies for a 4-day battle to test their cybersecurity skills against the National Security Agency’s (NSA) top information assurance professionals. West Point’s win comes just as the academy announced plans for its Army Cyber Institute(ACI), intended to develop elite cyber troops for the Pentagon.
-
-
How the Heartbleed bug reveals a flaw in online security
The Heartbleed bug – which infects an extremely widespread piece of software called OpenSSL — has potentially exposed the personal and financial data of millions of people stored online has also exposed a hole in the way some security software is developed and used. The Heartbleed bug represents a massive failure of risk analysis. OpenSSL’s design prioritizes performance over security, which probably no longer makes sense. But the bigger failure in risk analysis lies with the organizations which use OpenSSL and other software like it. A huge array of businesses, including very large IT businesses with the resources to act, did not take any steps in advance to mitigate the losses. They could have chosen to fund a replacement using more secure technologies, and they could have chosen to fund better auditing and testing of OpenSSL so that bugs such as this are caught before deployment. They didn’t do either, so they — and now we — wear the consequences, which likely far exceed the costs of mitigation.
-
-
Hacked U.S. surveillance drone over Crimea shows new face of warfare

A recent report of a U.S. surveillance drone flying over the Crimea region of Ukraine being hacked by Russian forces, is just one of many indication that the twenty-first-century global battlefield will take place in cyberspace. Radio and other frequencies which cover the electromagnetic spectrum are the new contested domain.
-
-
British intelligence agency promotes cybersecurity education
As part of its national cybersecurity strategy to “derive huge economic and social value from a vibrant, resilient, and secure cyberspace,” the United Kingdom will issue certifications to colleges and universities offering advanced degrees in cybersecurity. The British intelligence agency, Government Communications Headquarters(GCHQ), has notified various institutions to apply for certification by 20 June 2014. Students who complete the approved courses will carry a “GCHQ-certified degree.”
-
-
How computer worms are spreading among smartphones
Researchers have recently discovered that some of the most common activities among smartphone users — scanning 2D barcodes, finding free Wi-Fi access points, sending SMS messages, listening to MP3 music, and watching MP4 videos — can leave devices vulnerable to harmful “computer worms.” These worms can infiltrate smartphones through apps designed in a specific computer language/code — and they can do more harm than just steal the device owner’s personal information, researchers warn. They can also spread to the owner’s friends and personal contacts.
-
-
Feds struggle to plug power grid security holes
Many of the current vulnerabilities in the power grid are attributable to newly adopted smart-grid technology, which allows operators to transmit energy from a diverse pool of resources. Smart-grid technology relies on devices in remote locations which constantly communicate with substations, those access points can be compromised by hackers.
-
-
DHS repairing internal security operations
Last week DHS announced plans to overhaul its security operations center (SOC), the organization which protects DHS’ internal networks, and deploy a Next Generation Enterprise Security Operations Center (NextGen ESOC) which will incorporate state-of-the-art SOC technologies, concepts, and capabilities to address future security needs.
-
-
Measuring smartphone malware infection rates
Researchers show that infection rates in Android devices at around 0.25 percent are significantly higher than the previous independent estimate. They also developed a technique to identify devices infected with previously unknown malware.
-
-
Student develops new way to detect hackers
A Binghamton U student and her teammates are working on developing a new hacking detection solution. Instead of reviewing all programs run by a network to find the signature of one of millions of known malware programs — some of which mutate to avoid detection — they have developed a technology to assess behavior of individual computers. This is done by monitoring system calls, the internal signals that accompany every computer operation and can reveal every function performed by the computer.
-
-
U.S. Cyber Challenge opens registration for Cyber Quests competition
Last week the Council on CyberSecurity, through the U.S. Cyber Challenge (USCC) initiative, announces the open registration of its qualifying Cyber Quests competition — a challenging online contest open to high school and college students, as well as professionals, who will compete against their peers across the country for an invitation to one of four Cyber Camps being offered this summer. The online competition and camps are designed to improve cybersecurity skills, provide training and mentorship from leading instructors and highlight skills for potential employers.
-
-
Making quantum cryptography suitable for mobile phones
Secure mobile communications underpin our society and through mobile phones, tablets and laptops we have become online consumers. The security of mobile transactions is obscure to most people but is absolutely essential if we are to stay protected from malicious online attacks, fraud and theft. Researchers have shown how it is possible to make the resources necessary for quantum cryptography less bulky and expensive, and thus more suitable for mobile handsets.
-
- All
- Regional
- Water
- Biometrics
- Borders/Immig
- Business
- Cybersecurity
- Detection
- Disasters
- Government
- Infrastructure
- International
- Public health
- Public Safety
- Communication interoperabillity
- Emergency services
- Emergency medical services
- Fire
- First response
- IEDs
- Law Enforcement
- Law Enforcement Technology
- Military technology
- Nonlethal weapons
- Nuclear weapons
- Personal protection equipment
- Police
- Notification /alert systems
- Situational awareness
- Weapons systems
- Sci-Tech
- Sector Reports
- Surveillance
- Transportation
Advertising & Marketing: advertise@newswirepubs.com
Editorial: editor@newswirepubs.com
General: info@newswirepubs.com
2010-2011 © News Wire Publications, LLC News Wire Publications, LLC
220 Old Country Road | Suite 200 | Mineola | New York | 11501
Permissions and Policies
Editorial: editor@newswirepubs.com
General: info@newswirepubs.com
2010-2011 © News Wire Publications, LLC News Wire Publications, LLC
220 Old Country Road | Suite 200 | Mineola | New York | 11501
Permissions and Policies
