-
Russian govt. behind attack on Ukraine power grid: U.S. officials
Obama officials said that Russian hackers were behind a December 2015 cyberattack on Ukraine’s power grid. The attack caused power outages and blackouts in 103 cities and towns across Ukraine. Elizabeth Sherwood-Randall, deputy Energy Secretary, made the comments to a gathering of electric power grid industry executives.
-
-
Encryption prevents FBI from cracking San Bernardino attackers’ phone
U.S. law enforcement agencies have been unable to access a telephone used by the two Islamist attackers in the San Bernardino shooting, FBI director James Comey said Tuesday. Comey stressed that the post-Snowden end-to-end encryption some technology companies are now offering their customers make it impossible for law enforcement to learn more about terrorists and criminal networks, even after terrorist or criminal acts have been committed and even if a court has approved access to the information.
-
-
Intelligence agencies could use Internet-of-things to spy on people
James Clapper, the director of U.S. national intelligence, told lawmakers the other day that the Internet of things — baby monitors, TV set, home security devices, voice recognition dolls – may be used by intelligence services to spy on people. Clapper, testifying yesterday before a Senate panel, said that intelligence agencies might be able to use this new generation of household devices to increase their surveillance capabilities.
-
-
U.S. officials: DHS, DOJ hack not serious
Informed U.S. officials have downplayed the impact of the latest breach of government data in the wake of a hack of the employee information of 29,000 Department of Justice and DHS staff. Unidentified hackers on Sunday claimed that they had stolen personal information of about 20,000 DoJ employees — including FBI officials — and 9,000 DHS employees. Observers note that while the DHS breach is less severe than the one at OPM, it is still embarrassing for a department designated as the point of entry for all corporate data shared with government agencies in the information sharing program between industry and government created last year by the Cybersecurity Information Sharing Act.
-
-
Vulnerability found in in two-factor authentication
Two-factor authentication is a computer security measure used by major online service providers to protect the identify of users in the event of a password loss. Security experts have long endorsed two-factor authentication as an effective safeguard against password attacks. But what if two-factor authentication could be cracked not by computer engineering but by social engineering?
-
-
Hyperion cyber security technology receives commercialization award
The commercial licensing of a cybersecurity technology developed at the Department of Energy’s Oak Ridge National Laboratory has been recognized by the Federal Laboratory Consortium for Technology Transfer (FLC) as a good example of moving technology to the marketplace. Hyperion, which has the capability automatically to analyze executable programs and recognize behaviors that signal malicious intent and vulnerabilities, was licensed to Virginia-based R&K Cyber Solutions, LLC, in late 2014.
-
-
Realistic data needed to develop the 21st century power grid

Say you have a great new theory or technology to improve the nation’s energy backbone — the electric grid. Would it not be great to test it against a model complete with details that would tell you how your ideas would work? But it is a challenge, because existing sets of data are too small or outdated; and you do not have access to real data from the grid because of security and privacy issues. To overcome this problem, is helping to create open-access power grid datasets for researchers and industry.
-
-
Reframing the encryption debate
A new report examines the high-profile debate around government access to encryption, and offers a new perspective gleaned from the discussion, debate, and analyses of an exceptional and diverse group of security and policy experts from academia, civil society, and the U.S. intelligence community. The report takes issue with the usual framing of the encryption debate and offers context and insights that widen the scope of the conversation more accurately to reflect the surveillance landscape both now and in the future.
-
-
Building cyber security testbed to help protect the power grid
It is easy to think of the electrical grid as the power plants, the high voltage lines, the transmission towers, the substations, and all the low-voltage distribution lines that bring power to our homes and businesses. An attack on that grid would involve getting out and cutting lines or dropping towers. But there is another, less visible piece to the grid — all the computers and communication networks that make it work. Attackers can go after the cyber grid, too. They can do it from a desktop. At no real cost. Potentially from anywhere in the world. With few if any clues left behind.
-
-
NIST seeks vendors to help secure wireless medical devices
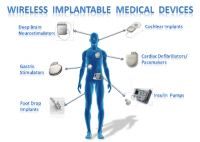
Medical devices such as the infusion pumps that deliver medication intravenously were once standalone instruments that interacted only with the patient. Today, they have operating systems and communications hardware that allow them to connect to other devices and networks. While this technology has created more powerful tools and the potential for improved patient care, it also creates new safety and security risks.
-
-
Researchers use advanced algorithms to identify six botnets
Ben-Gurion University of the Negev (BGU) cyber security researchers have discovered and traced approximately six “botnets” by analyzing data collected from past cyberattacks. Botnets are networks of malicious, remotely updatable code that covertly lurk on infected computers.
-
-
Navigations systems are vulnerable to hackers
When it comes to route planning, drivers have almost blind faith in GPS. The technology plays an important role in identifying location and time in other areas, too. If hackers attack the system, they can cause great damage. Information security researches look to develop defensive measures.
-
-
Using unpredictability to defend computers from cyberattacks
We want our computers to perform the way we expect. But what if the key to defeating malware is introducing a bit of chaos? Researchers think a bit of unpredictability could help outsmart malware. This is the logic behind Chameleon, the operating system they are developing. In Chameleon, which is still in the conceptual phase, unknown programs that could be malware run in a special “unpredictable” environment, where the OS intentionally introduces some unpredictability to the way they operate.
-
-
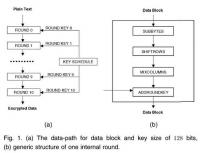
Intel unveils new security-on-a-chip system
Intel on Tuesday unveiled a new password security-on-a-chip system called Intel Authenticate. The new security system aims to thwart hackers who use fake e-mails to trick employees into revealing sensitive information like user names and passwords. Intel said that putting the authentication process on a chip makes the PC itself part of the security system.
-
-
U Wyoming could become cybersecurity hub

Wyoming Governor Matt Mead has requested state funding to develop a program at the University of Wyoming to become a center of excellence in cyber defense. According to the Wyoming Cybersecurity Education Initiative, proposed curriculum in the College of Engineering and Applied Science’s Department of Computer Science would educate students to defend against such attacks and “provide meaningful and sustainable impact to Wyoming’s technology sector through cybersecurity and information assurance higher-education programs.”
-
More headlines
The long view
What Does Netflix’s Drama “Adolescence” Tell Us About Incels and the Manosphere?
While Netflix’s psychological crime drama ‘Adolescence’ is a work of fiction, its themes offer insight into the very real and troubling rise of the incel and manosphere culture online.
Confronting Core Problems in Cybersecurity
It’s common for governors and mayors to declare a state of emergency and activate the National Guard in the aftermath of hurricanes, tornadoes, and other natural disasters. But last month, officials in Minnesota took these steps in the wake of a major cyberattack on the city of St. Paul —a testament to how disruptive these attacks have become.
Voting from Your Sofa Is Secure Enough – but Will It Be Allowed?
A new electronic voting system developed at NTNU can withstand attacks from quantum computers, meaning digital elections can be conducted securely, even in the future.
