-
McAfee releases 2012 cyber threat predictions

The cyberthreats organizations and individuals are likely to face in 2012 will resemble those they faces in 2011, only more so; among the increased threats: attacks on critical infrastructure, mobile devices and consumer electronics, and politically motivated attacks
-
-
DHS social media monitoring policy under fire
DHS’ tactics of gathering intelligence via social media has drawn sharp criticism from privacy advocates with one group filing a lawsuit against the department
-
-
Lieberman asks Twitter to shut down Taliban accounts

Senator Joe Lieberman (I-Connecticut), the chair of the Homeland Security Committee, has requested that the popular social media site Twitter shut down the accounts of the Taliban
-
-
DHS, Idaho lab win cybersecurity innovation award
The Controls Systems Security Program (CSSP) at DHS and Idaho National Laboratory have created a series of training programs for managerial and technical people in the critical infrastructure sector that are packed with up-to-date information on cyber threats and mitigations for vulnerabilities
-
-
Anonymous threatens Internet blackout over controversial legislation

The hacker group Anonymous has vowed to blackout the Internet if U.S. lawmakers pass the controversial Stop Online Piracy Act; under the bill, government powers would be greatly expanded, enabling the Justice Department working at the behest of individual copyright holders to shut down Web sites for potential copyright violations
-
-
Lawmaker targets fake ID smartphone app
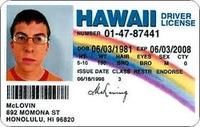
With the “License” app for Apple iPhones and iPads, making a realistic fake ID has never been easier; to prevent this app from falling into the wrong hands that would use it for nefarious purposes, Senator Bob Casey (D — Pennsylvania) recently requested that Apple remove the app from its online store
-
-
National Guardsmen, the new front line in cybersecurity

In an aggressive push to expand the military’s cyber warfare and defense capabilities, the National Guard has formed an increasing number of special cybersecurity units; National Guard cybertroops have proven to be particularly appealing solution, especially with defense cuts looming, as they cost less to train, maintain, and retain than active duty forces
-
-
Twelve Chinese hacker groups responsible for attacks on U.S.

U.S. cybersecurity experts say as few as twelve different Chinese hacker collectives, working at the behest of the government, are responsible for the majority of cyberattacks on U.S. businesses and government agencies; the bulk of the attacks are stealthy in nature and have resulted in the loss of billions of dollars’ worth of intellectual property and state secrets from the private and public sector
-
-
Electrical grid needs cybersecurity oversight: study

In a recently released report, researchers from the Massachusetts Institute of Technology say that a single federal agency should be tasked with protecting the United States’ electrical grid from cyberattacks; the Obama administration has proposed that DHS assume responsibility for the grid, while Congress has submitted proposals for both the Department of Energy and the Federal Energy Regulatory Commission (FERC)
-
-
MIT report warns U.S. electrical grid vulnerable
A new report from the Massachusetts Institute of Technology warns that the U.S. electrical grid is vulnerable to cyberatacks; according to the report, the U.S. electrical grid’s cybersecurity vulnerabilities stem from weaknesses in processes, technology, as well as the actual physical environment
-
-
Shell fears cyberattack on oil infrastructure
Oil executives fear that a cyberattack on critical infrastructure could wreak havoc by destroying facilities or disrupting production
-
-
Government outlines cybersecurity R&D priorities
The Obama administration recently unveiled its plan for government sponsored cybersecurity research and development programs
-
-
SCADA systems’ vulnerability key weakness in Smart Grid deployments
The discovery of the Stuxnet worm in 2010 shone a harsh light on the fragility of industrial control systems (ICS), such as supervisory control and data acquisition (SCADA) systems, and has created a new urgency among security vendors and utility managers alike; new research forecasts that investments in ICS security will total $4.1 billion during the years between 2011 and 2018
-
-
$3 million NSF grant for research into assured data provenance
The National Science Foundation supports funds new cyber security research into assured data provenance, the discipline of computer science concerned with the integrity and privacy of data sources, contents, and successive transformations
-
-
Cyber security measure requires more information sharing
The Cyber Intelligence Sharing and Protection Act of 2011 (H.R. 3523) made it through the House Permanent Select Committee on Intelligence on 1 December on a 17-1 vote. It is one of a dozen or so cyber security-related legislative initiatives proposed by lawmakers this year. The effort is bipartisan, having been introduced by committee chairman Mike Rogers (R-Michigan) and ranking member Dutch Ruppersberger (D-Maryland). The bill aims to promote greater information sharing between the federal government and U.S. businesses.
-
More headlines
The long view
Encryption Breakthrough Lays Groundwork for Privacy-Preserving AI Models
In an era where data privacy concerns loom large, a new approach in artificial intelligence (AI) could reshape how sensitive information is processed. New AI framework enables secure neural network computation without sacrificing accuracy.
Need for National Information Clearinghouse for Cybercrime Data, Categorization of Cybercrimes: Report
There is an acute need for the U.S. to address its lack of overall governance and coordination of cybercrime statistics. A new report recommends that relevant federal agencies create or designate a national information clearinghouse to draw information from multiple sources of cybercrime data and establish connections to assist in criminal investigations.
