-
McAfee, Intel collaborate on protecting energy infrastructure

McAfee and Intel will collaborate on improving the protection of the world’s energy utilities, including generation, transmission, and distribution, from increased cyber attacks; the two companies have provided a blueprint for a comprehensive solution of multiple products which create layers of security and operate together without great complexity or without impacting availability
-
-
Self-adapting computer network that actively defends itself against hackers
Researchers are looking into the feasibility of building a computer network that could protect itself against online attackers by automatically changing its setup and configuration; the researchers will examine whether this type of adaptive cybersecurity, called moving-target defense, can be effective – and cost-effective
-
-
Travelers’ laptops infected through fake software updates in foreign hotel rooms
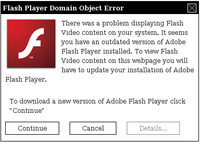
Recent analysis from the FBI and other government agencies demonstrates that malicious actors are targeting travelers abroad through pop-up windows while establishing an Internet connection in their hotel rooms
-
-
Number, diversity of targeted cyberattacks increased in 2011
The number of vulnerabilities decreased by 20 percent in 2011, but the number of malicious attacks leaped by 81 percent in the same period; targeted attacks have spread to organizations of all sizes and types
-
-
Slowing time as a way to counter cyberattacks
Researchers offer a new way to deal with cyberattacks on critical infrastructure like power and water utilities and banking networks: slow down Internet traffic, including the malicious code, when an attack is suspected; this would allow networks time to deal with the attacks
-
-
NATO prepares for a new, futuristic war
NATO’s Operation Locked Shields, an international military exercise the military alliance conducted last month, was different from trasditional war games. There were no bullets, tanks, aircraft, ships, or camouflage face-paint. The troops involved in the exercise spent most of their time in air-conditioned rooms within a high security military base in Estonia. The exercise, a window into what a future war would look like, had one team of IT specialists detailed to attack nine other teams, located in different parts of Europe. The IT experts, working from their terminals in the Nato Co-operative Cyber Defense Center of Excellence, created viruses, worms, Trojan Horses, and other Internet attacks, aiming to hijack and extract data from the computers of their “enemies.”
-
-
Facebook, antivirus providers in Internet security campaign
Facebook, Microsoft, McAfee, Symantec, Trend Micro, and Sophos have joined in a campaign to make it easier for Facebook users to stay safer and more secure online
-
-
Cyberattack disrupts Iran’s oil production system
The Iranian oil industrywas subject to cyber attack this past weekend,but the Iranian government saysit has contained and controlled the damage from the malware; this is the fourth known cyber attack on Iran’s civilian and military infrastructure
-
-
Better cybersecurity for the healthcare industry
Healthcare organizations face ever more threatening cyber attacks. In response, the Health Information Trust Alliance (HITRUST) has established the HITRUST Cybersecurity Incident Response and Coordination Center to provide support for the healthcare industry
-
-
Global CyberLympics Games agreement announced
Organizations announce 2-year agreement to conduct the CyberLympics Games, a series of global cyber games held on six continents and aiming to raise awareness of information security and unifying global cyber defense
-
-
Closing digital security gaps
Two European research centers, one German the other from Luxemburg, have recently agreed on a mutual course for the strategic development of new and integrative approaches to addressing key IT security concerns
-
-
Feds recruit companies to aid in cyberdefense
The U.S. national security community is intensifying its efforts to enlist the aid of the private security sector in bolstering the U.S. cyberdefenses
-
-
Companies hiring hackers to harden defenses

To burglar-proof your home, it is best hire a burglar as a consultant, as he is more likely to find the security vulnerabilities and demonstrate how they can be exploited; following this approach, companies large and small are now hiring hackers to test the companies’ security system vulnerabilities and find ways to harden these systems to withstand intrusion
-
-
WWII-like message encryption now available for e-mail security

A Singapore-based company offers an e-mail encryption system based on the Verman cipher, or one-time pad, which was invented in 1917 and used by spies in the Second World War; the Vernam cipher is unbreakable because it produces completely random cipher-text that secures data so that even the most powerful super computers can not break the encryption when it is used properly
-
-
Industry insiders: insufficient security controls for smart meters
False data injection attacks exploit the configuration of power grids by introducing arbitrary errors into state variables while bypassing existing techniques for bad measurement detection; experts say current generation of smart meters are not secure enough against false data injection attacks
-
More headlines
The long view
Ransomware Attacks: Death Threats, Endangered Patients and Millions of Dollars in Damages
A ransomware attack on Change Healthcare, a company that processes 15 billion health care transactions annually and deals with 1 in 3 patient records in the United States, is continuing to cause massive disruptions nearly three weeks later. The incident, which started on February 21, has been called the “most significant cyberattack on the U.S. health care system” by the American Hospital Association. It is just the latest example of an increasing trend.
Chinese Government Hackers Targeted Critics of China, U.S. Businesses and Politicians
An indictment was unsealed Monday charging seven nationals of the People’s Republic of China (PRC) with conspiracy to commit computer intrusions and conspiracy to commit wire fraud for their involvement in a PRC-based hacking group that spent approximately 14 years targeting U.S. and foreign critics, businesses, and political officials in furtherance of the PRC’s economic espionage and foreign intelligence objectives.
Autonomous Vehicle Technology Vulnerable to Road Object Spoofing and Vanishing Attacks
Researchers have demonstrated the potentially hazardous vulnerabilities associated with the technology called LiDAR, or Light Detection and Ranging, many autonomous vehicles use to navigate streets, roads and highways. The researchers have shown how to use lasers to fool LiDAR into “seeing” objects that are not present and missing those that are – deficiencies that can cause unwarranted and unsafe braking or collisions.
