-
Stuxnet and Duqu part of assembly line: researchers

Stuxnet, the highly sophisticated piece of malicious code that was the first to cause physical damage, could just be the tip of the iceberg in a massive cyberweapon manufacturing operation; according to cybersecurity researchers at Kaspersky Labs and Symantec, Stuxnet appears to be part of a larger cybersecurity weapons program with fully operational and easily modified malicious code that can be aimed at different targets with minimal costs or effort
-
-
Hackers continue cyberwar against Israel
As part of an intensifying cyberwar against Israel, on Monday hackers brought down several key websites including the Tel Aviv Stock Exchange, the national airline, and three banks
-
-
Chinese hackers target DoD, DHS smart cards
Cybersecurity researchers have discovered malicious code developed by Chinese hackers to target the smart cards used by Defense Department, DHS, and State Department personnel
-
-
Gender gap hinders cybersecurity hiring boom
As governments and private businesses clamor to hire computer experts, women are conspicuously missing from the employment boom; women account for over half the professional workforce, yet only 25 percent of information technology jobs are filled by females
-
-
Delaware student takes top prize at annual cyber competition
The U.S. Cyber Challenge recently announced the results of its annual Fall Cyber Foundations competition with the top honors going to Gavy Aggrawal, a sophomore at Delaware’s Charter School of Wilmington
-
-
Japan develops anti-hacker weapon
The Japanese Ministry of Defense recently revealed that it is developing a new weapon to combat hackers – a “seek and destroy” virus designed to track and disable the source of cyber-attacks
-
-
ETrade cyberattack shuts down trading
Over the holiday season, Australia’s second-largest online brokering service, ANZ Bank’s ETrade was hit by a series of cyberattacks, temporarily locking out customers
-
-
Government contractors now required to have cybersecurity plans
Based on a new General Services Administration (GSA) rule, all contractors and subcontractors that provide federal agencies with IT services, systems, or supplies are required to submit a cyberescurity plan that matches government regulations
-
-
UMD, Lunarline partner on cybersecurity
The University of Maryland Cybersecurity Center will partner with Lunarline Inc. on cybersecurity education, research, and technology development
-
-
Wireless passwords vulnerable to hackers, US-CERT warns
The U.S. government is warning wireless users that their home and business networks are highly vulnerable to hackers
-
-
Smartphone users hold false sense of security
A recent study reveals that smartphone users maintain a false sense of cybersecurity
-
-
McAfee releases 2012 cyber threat predictions

The cyberthreats organizations and individuals are likely to face in 2012 will resemble those they faces in 2011, only more so; among the increased threats: attacks on critical infrastructure, mobile devices and consumer electronics, and politically motivated attacks
-
-
DHS, Idaho lab win cybersecurity innovation award
The Controls Systems Security Program (CSSP) at DHS and Idaho National Laboratory have created a series of training programs for managerial and technical people in the critical infrastructure sector that are packed with up-to-date information on cyber threats and mitigations for vulnerabilities
-
-
Anonymous threatens Internet blackout over controversial legislation

The hacker group Anonymous has vowed to blackout the Internet if U.S. lawmakers pass the controversial Stop Online Piracy Act; under the bill, government powers would be greatly expanded, enabling the Justice Department working at the behest of individual copyright holders to shut down Web sites for potential copyright violations
-
-
Lawmaker targets fake ID smartphone app
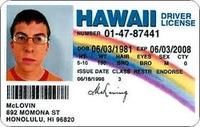
With the “License” app for Apple iPhones and iPads, making a realistic fake ID has never been easier; to prevent this app from falling into the wrong hands that would use it for nefarious purposes, Senator Bob Casey (D — Pennsylvania) recently requested that Apple remove the app from its online store
-
More headlines
The long view
Ransomware Attacks: Death Threats, Endangered Patients and Millions of Dollars in Damages
A ransomware attack on Change Healthcare, a company that processes 15 billion health care transactions annually and deals with 1 in 3 patient records in the United States, is continuing to cause massive disruptions nearly three weeks later. The incident, which started on February 21, has been called the “most significant cyberattack on the U.S. health care system” by the American Hospital Association. It is just the latest example of an increasing trend.
Chinese Government Hackers Targeted Critics of China, U.S. Businesses and Politicians
An indictment was unsealed Monday charging seven nationals of the People’s Republic of China (PRC) with conspiracy to commit computer intrusions and conspiracy to commit wire fraud for their involvement in a PRC-based hacking group that spent approximately 14 years targeting U.S. and foreign critics, businesses, and political officials in furtherance of the PRC’s economic espionage and foreign intelligence objectives.
Autonomous Vehicle Technology Vulnerable to Road Object Spoofing and Vanishing Attacks
Researchers have demonstrated the potentially hazardous vulnerabilities associated with the technology called LiDAR, or Light Detection and Ranging, many autonomous vehicles use to navigate streets, roads and highways. The researchers have shown how to use lasers to fool LiDAR into “seeing” objects that are not present and missing those that are – deficiencies that can cause unwarranted and unsafe braking or collisions.
